Android phones can be security keys now
Google looks to tackle one of the biggest problems with two-factor authentication: convenience.
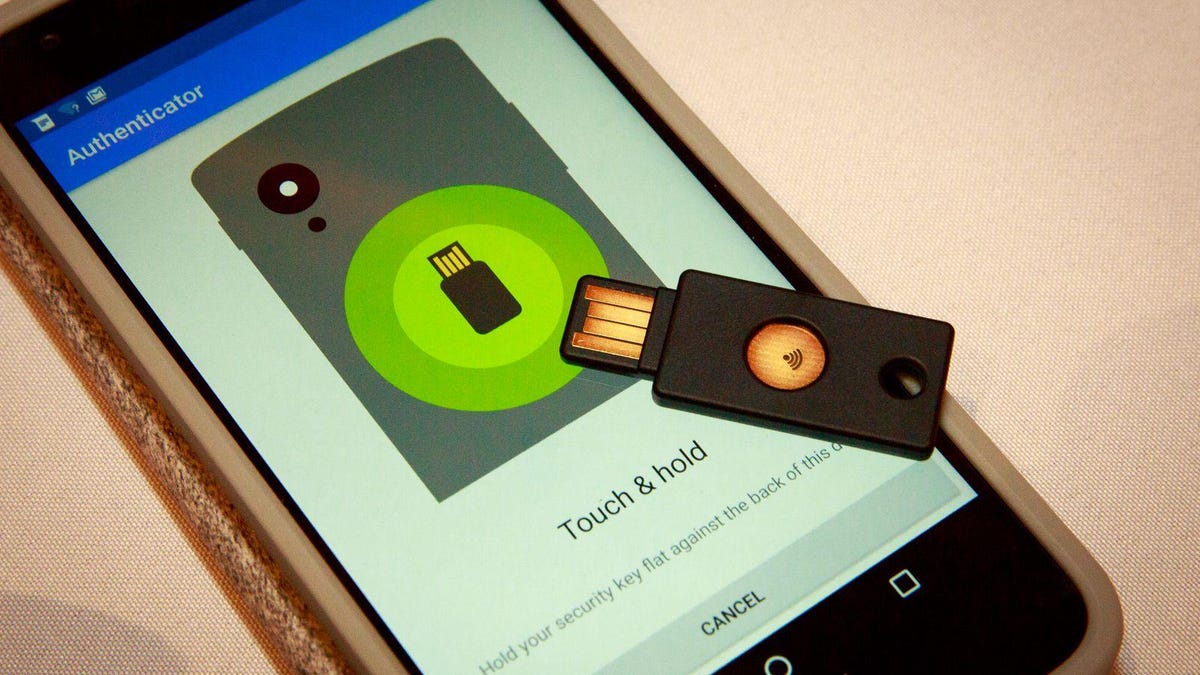
A physical security key on top of an Android phone.
Security keys are an effective way to keep your accounts secure from hackers, but they suffer from a major challenge: They're inconvenient.
Not a lot of people want to buy and carry an extra key or Bluetooth fob just for logging in -- which is why most two-factor authentication is done through text messages, even though it's less secure. Up to 90% of Gmail users don't even use 2FA, a Google software engineer revealed in 2018.
Convenience is a big hurdle, and Google is hoping to solve that by making your phone the security key. It'll have the same functionalities as a physical security key but won't require you to carry an extra device to keep your accounts safe.
That means that like a security key, your phone will warn you if an imposter website is trying to steal your password. Unlike using SMS or authenticator codes for logging in, security keys have to verify that the website you're logging in on is legitimate.
The updated security feature is coming only to Android devices versions 7 and up, which account for about 50% of all active users, according to Google's distribution board. For now, it's working only on Google's Chrome browser and with Google accounts, but the company expects to expand availability.
"This is a natural evolution of the standard. Just as some security keys only worked with Chrome initially and moved to other browsers, we're seeing the same thing happening here," said Christiaan Brand, a Google product manager for identity and security.
You can set up the security key on your phone by going to your settings on Google and selecting 2-Step Verification. From there, you need to click on Add a Security Key and choose your phone as a device.
School of phish
Phishing attacks are common and often hard to spot, fooling even seasoned politicians. Security keys help prevent hackers from getting into your accounts because even if your password were stolen, an attacker would have to have the physical key to log in.
"We're solving the problem of someone thousands of miles away trying to steal your password," said Sam Srinivas, Google Cloud's product management director. "With this, someone has to be within 100 feet of you to try to attack you."
When Google first released its own Titan Key, it cost $50 for a set, and Brand said the company was hoping to eventually drive the cost down to less than $10.
Last year, Google released its own Titan Security Key in both a USB and Bluetooth version.
By turning Android devices into security keys, Google is essentially giving them out for free. That much coverage could make it easier for more people to start using security keys, said Conor Gilsenan, a security researcher at All Things Auth.
Over Christmas, the security expert said, he bought his family members security keys, but it took more than two hours to set up all these devices.
"This is such a big deal," Gilsenan said. "Being able to utilize the phone that you already have removes an entire barrier to better forms of two-factor authentication for the average internet user."
Brand said the phone security keys meet the FIDO authentication standard, which means any websites allowing for that standard will work with your phone as a security key. That includes websites like Facebook, Twitter and GitHub.
Convenience is key
Brand is hoping the launch will convince other pages to accept phones as security keys.
The technology works by connecting your phone and your computer's Bluetooth when you're logging in on a Google account. You'll be prompted with a message on your phone to verify the log-in once they're connected. While they're using Bluetooth to communicate, the two devices don't have to pair with each other, Brand said.
"We devised a new standard on top of Bluetooth to make sure that these don't need to pair," he explained.
There have been criticisms of using Bluetooth in security keys, because the wireless protocol could be open to security vulnerabilities. When Google announced its Bluetooth security fob last year, Yubico CEO Stina Ehrensvard released a statement saying Bluetooth didn't have the same security standards as NFC and USB.
Brand said Google had the capability to let your phone function as a security key through a USB cable but decided against it.
"We've done user studies, and asking a user to have a cable ready that'll fit both their devices almost takes away all the convenience of using their phone," he said.
Still, even with all the convenience of phones, Brand and Srinivas recommend having a second, backup USB key. That way, if you ever lose your phone or the battery's dead, you can still log in.
Now that half of all Android devices can function as security keys, the new challenge will be getting people to actually use them that way.
Security keys have a lower adoption rate than 2FA as a whole, but the convenience will likely draw more people to better protect their accounts.
"You don't have to plug it in, and you don't have to buy a new device, since you already have the phone," Gilsenan said. "The bigger challenge is communicating to people that they actually need 2FA."

