Quantum computers could crack today's encrypted messages. That's a problem
We'll likely see the top picks for safer, post-quantum encryption technology early in 2022.
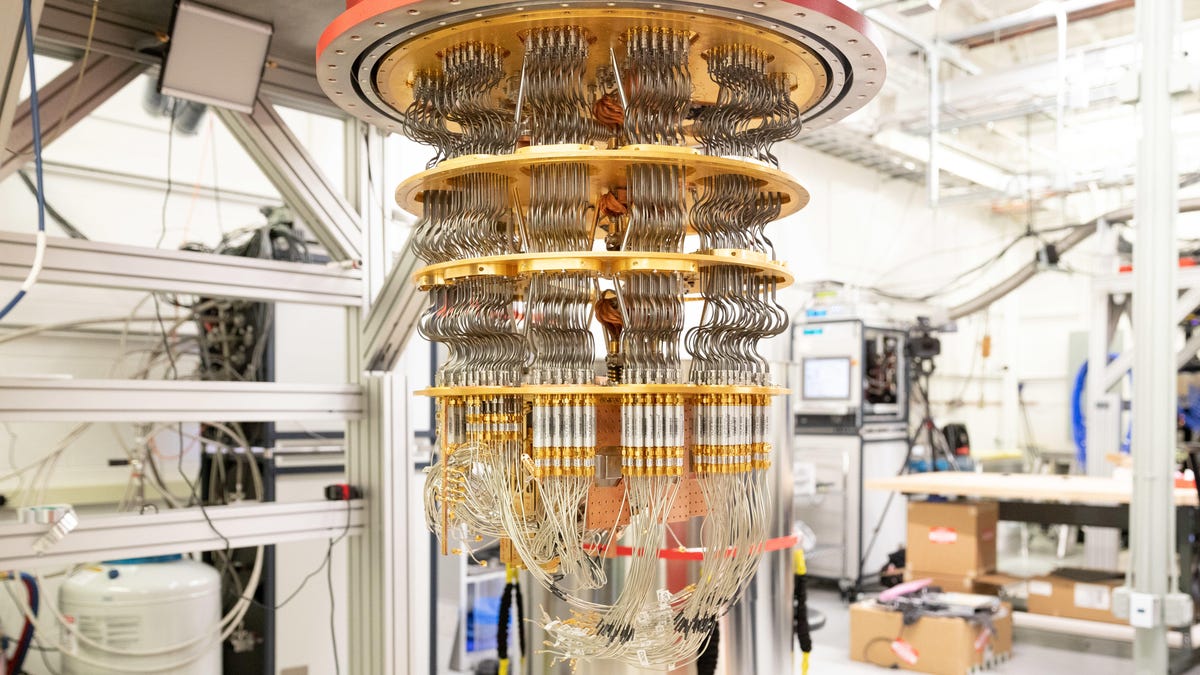
Google plans to make million-qubit quantum computers by 2029 that are much more powerful than this system it showed in 2019.
Quantum computers, if they mature enough, will be able to crack much of today's encryption. That'll lay bare private communications, company data and military secrets.
Today's quantum computers are too rudimentary to do so. But data surreptitiously gathered now could still be sensitive when more powerful quantum computers come online in a few years.
The computing industry is well aware of this potential vulnerability. Some companies have embarked on an effort to create, test and adopt new encryption algorithms impervious to quantum computers. Some of those companies, including IBM and Thales, have already begun offering products protected by what's called post-quantum cryptography.
Quantum-safe encryption will come into your life through upgraded laptops, phones, web browsers and other products. But most of the burden for quantum-safe encryption rests on the shoulders of businesses, governments and cloud computing services that must design and install the technology. It's an extraordinarily complex change that's on par with fixing Y2K bugs or upgrading internet communications from IPv4 to IPv6.
It's a colossal effort, but it has to be done. Not only are today's communications vulnerable, but quantum computers later could crack the digital signatures that ensure the integrity of updates to apps, browsers, operating systems and other software, opening a path for malware.
Quantum computing is the darling of the industry, and it's attracted millions of dollars in investment. At this month's Google I/O developer conference, the search giant unveiled plans for a new quantum computing center that will employ hundreds of people with the goal of building a practical quantum computer by 2029. Other tech giants, such as Honeywell, IBM, Intel and Microsoft, are racing to build the first powerful quantum computers. So are IonQ, PsiQuantum, Xanadu, Silicon Quantum Computing and other startups.
Finding post-quantum crypto algorithms
The US National Institute of Standards and Technology is spearheading the global effort to find post-quantum cryptography algorithms that will be fast and trustworthy. It's winnowed 82 initial contributions down to a group of seven final candidates for two encryption tasks: exchanging digital keys and adding digital signatures.
"We expect toward the start of 2022 or so, we will select a small number of them to begin being standardized," Dustin Moody, a NIST mathematician working on the effort, said at an IBM cryptography meeting in March. "We hope to have the final version completely ready and published around 2024."
Though NIST oversees the work, researchers from business, academia and the government are participating through NIST's post-quantum cryptography mailing list and public PQC conferences. The open approach is important since encryption algorithms require deep scrutiny before we can trust them to protect our passwords, credit card numbers, financial records and other sensitive information.
When these machines will be able to crack conventional encryption is an open question. But the safe money suggests it won't take long.
John Graham-Cumming, chief technology officer of internet infrastructure company Cloudflare, said there's a lot of uncertainty: It could take five years before quantum computers can crack encryption or it could take 20. But already Cloudflare has tested post-quantum protections and plans to adopt them for internal operations this year.
Researchers at Intel and NTT Research and 451 Research analyst James Sanders reckon it will take on the order of a decade.
How urgent is fixing the problem?
"I'm not quite hair on fire," said Brian LaMacchia, who leads encryption work at Microsoft Research. "But I'm a little singed."
Harvest data now, crack it later
The urgency comes because today's encrypted data could be collected now and cracked later. Hackers or nations can record network data, for example, when internet routing problems send traffic across borders to China or other nations.
"If you want long-term security, it might even be too late," said Thomas Pöppelmann, a cryptography engineer at German chipmaker Infineon and co-creator of one of the PQC algorithm candidates.
NIST has a blunt assessment of the problem. When cyber adversaries have access to the power of quantum computing, our modern cryptographic systems based on public keys won't stand up to the test. "Nothing can be done to protect the confidentiality of encrypted material that was previously stored by an adversary," the agency says.
Public key cryptography is the foundation for much of today's encryption. It pairs two digital keys, one secret and one public, that together can be used to secure communications. For example, it's used to establish the security of connections between your web browser and your bank or between a company server and a remote backup system.
Shor's algorithm and cracking encryption
In 1994, Peter Shor, a professor at MIT, figured out that quantum computers could find the prime factors of numbers through a technique now named after him. Shor's algorithm was the spark that ignited quantum computing interest from companies, academics and intelligence agencies, says Seth Lloyd, another MIT professor and a pioneer of the field.
The resulting research is why major companies and well-funded startups are picking up the pace of their quantum computing progress. Quantum computer makers are building machines with more and more qubits -- their fundamental data processing elements -- while developing error correction techniques to keep them stable through longer calculations. Algorithms are speeding up quantum computer decryption, too.
Accelerating quantum computing progress
The quantum computing progress led cybersecurity firm Deepwatch to speed up its timetable for encryption cracking. Instead of taking 20 years, it could happen in 10 to 15 years, said Marissa "Reese" Wood, vice president of product and strategy.
For today's ubiquitous RSA encryption algorithm, a conventional computer would need about 300 trillion years to crack communications protected with a 2,048-bit digital key. But a quantum computer powered by 4,099 qubits would need just 10 seconds, Wood said.
For comparison, Google hopes to build a quantum computer in 2029 with 1,000 "logical" qubits -- ones stable enough to perform a long calculation.
What to do about post-quantum encryption
The quantum transition is in many ways harder than some past encryption upgrades. One problem is that digital key sizes likely will be larger, requiring more memory to process them. Changing algorithms won't be a simple swap, especially for smart home devices and other products with limited computing horsepower.
Even before NIST picks its winners, companies can embrace "crypto agility" in today's computing infrastructure, ensuring their systems aren't reliant on a particular encryption technology. That's the advice of several experts, including Andersen Cheng, chief executive officer of Post-Quantum, a London-based company that helps customers deal with quantum cracking.
"People thought I was mad" when he co-founded Post-Quantum in 2009, Cheng said. "I don't think they're laughing anymore."
Experts also recommend a hybrid approach that double-protects data with both conventional and post-quantum security encryption. That lets system administrators embrace PQC sooner without worrying as much about weaknesses that could be found in relatively immature algorithms. Hybrid encryption is possible now, though most expect serious adoption of PQC to take place after NIST is done with its standardization work.
IBM already offers quantum-safe crypto in several cloud computing products today. "If you have secrets which need to remain secret 10 to 30 years from now, you should begin this migration sooner than later," said IBM Research cryptography researcher Vadim Lyubashevsky.
France-based Thales, which like IBM has a PQC algorithm in NIST's final round, has begun letting clients test the technology. That's important given its clout with finance and government customers.
Not an easy upgrade
Switching to quantum-safe encryption in slower-moving computing infrastructure is harder.
"Estonian voting cards have a signature algorithm that's physically burned into a chip," said Joël Alwen, chief cryptographer at secure communications company Wickr. "That's going to be a huge effort to change that."
Another tough fix will be computer systems that control power grids and military operations. They typically run for decades. But wherever there's sensitive data, post-quantum cryptography upgrades will happen, said Gartner analyst Martin Reynolds.
"In 20 years," Reynolds said, "everyone will be glad we did it."

