Google warns Titan Security Key has Bluetooth bug that leaves it vulnerable
Hackers could exploit a flaw in how the company's security key pairs with a device over Bluetooth. Google is offering free replacement keys.
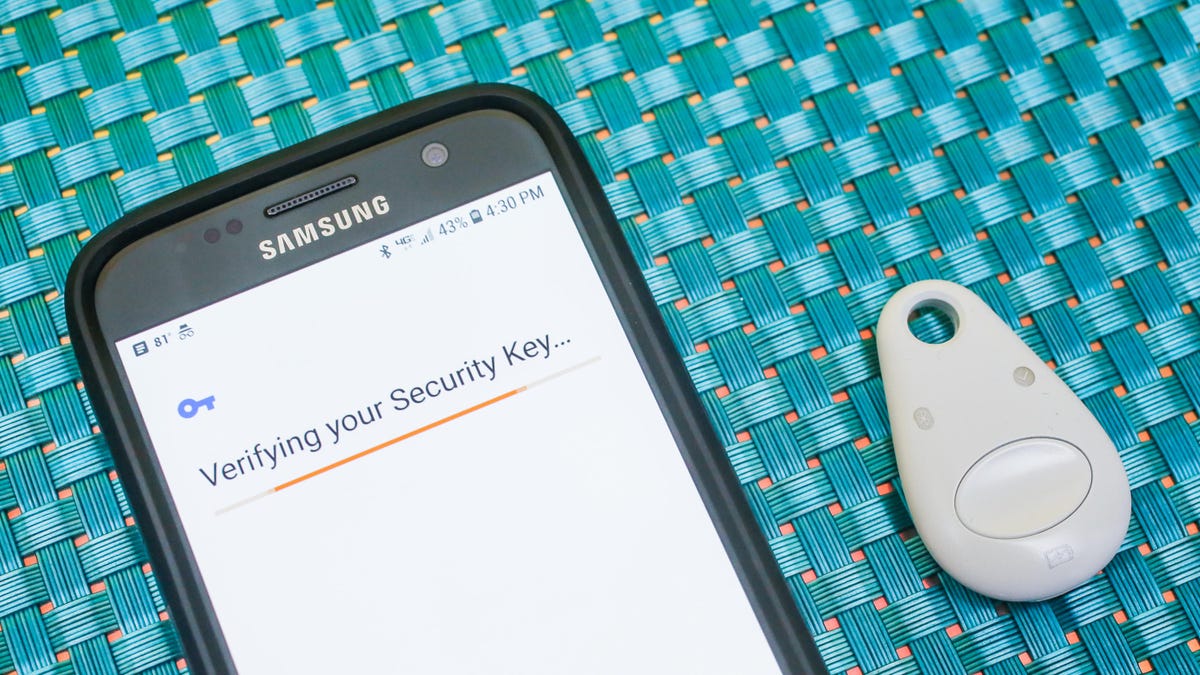
Google is offering a free replacement for the Bluetooth edition of its Titan Security Key.
Google's security key has a bug.
On Wednesday, Google issued a warning about its Titan Security Key, specifically the Bluetooth edition of the device. The key has a security bug in how it pairs with a device over Bluetooth, and how that pairing is authenticated.
A nearby attacker could rename any Bluetooth device with the Titan Security Key's name and trick a user into connecting to that fraudulent device instead. Once connected to the victim's gadget via Bluetooth, the hacker would be able to take actions on the machine, Google warned.
Google also noted another attack scenario, where a nearby attacker could connect to a person's Bluetooth security key before the real owner did. In that situation, if the attacker already knew the person's login credentials, the account would be accessible.
Google recommended unpairing the Bluetooth key and requesting a replacement. The company warned that if you're using the security key's Bluetooth pairing, you should make sure you're in a private place where a potential attacker couldn't be within 30 feet.
Security keys are generally an effective way to prevent account takeovers, but Google's disclosure on Wednesday provides examples of how hackers might still find ways around them. Still, this vulnerability requires an attacker to be nearby, and to orchestrate a targeted, coordinated hack.
"It is much safer to use the affected key instead of no key at all," Christiaan Brand, Google Cloud's product manager, said in the company's post about the bug. "Security keys are the strongest protection against phishing currently available."
You can check if your Titan Security Key is affected by looking for a "T1" or "T2" on the back of it. Google is offering a free replacement.
The Titan Key also comes in a USB form, which isn't affected by this bug.

