Why KRACK could hit your smart home's Wi-Fi the hardest
Smart devices and appliances, everything from your refrigerator to your television, are ideal targets for hackers thanks to the KRACK exploit.
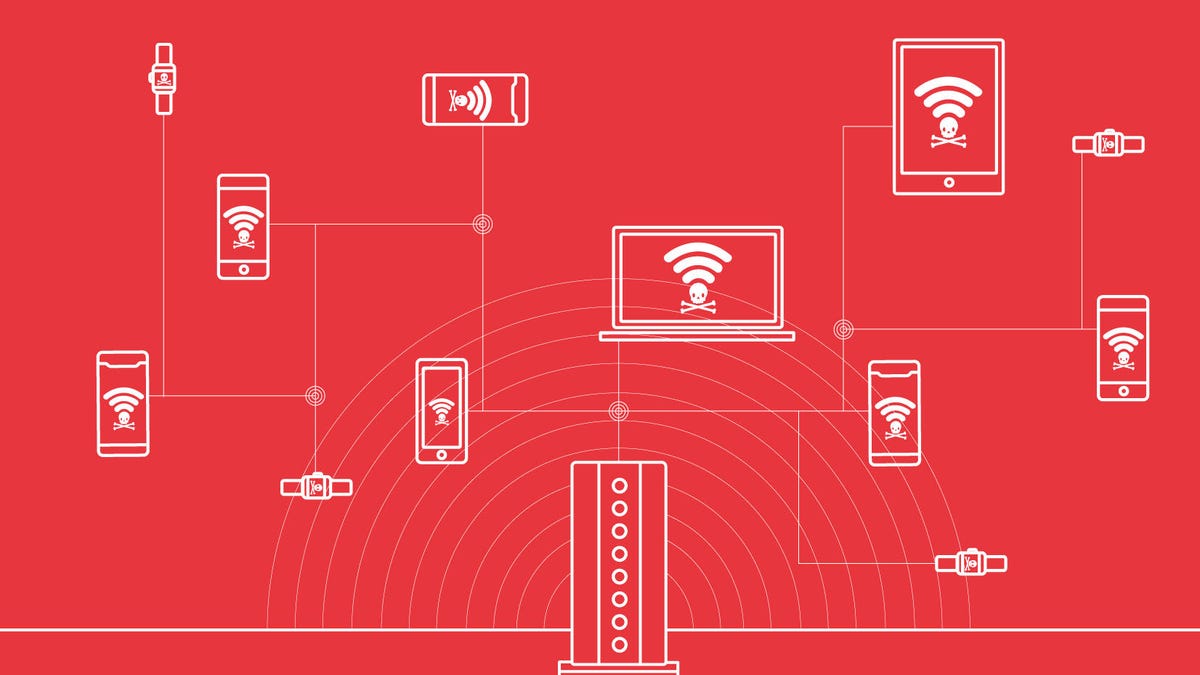
The KRACK attack hits any device using WPA2 security, and it may hit smart homes the hardest.
The latest massive security vulnerability hits close to home.
It's called KRACK, short for Key Reinstallation Attack, and it's a vulnerability that affects any Wi-Fi connection using the common encryption method WPA2. That means pretty much any device using Wi-Fi is fair game.
The good news is your phones and laptops are likely safer from attacks thanks to rapid security updates. The bad news: your smart home gadgets may not be so lucky.
The attack is the latest reminder of the pitfalls we face when it comes to our increasingly smart, connected devices. When your television and refrigerator hold sensitive information like Netflix or Amazon logins, they become potential targets for hackers. It's a problem that's going to get worse as the internet of things grows and we further surround ourselves with gadgets that talk to each other.
KU Leuven researchers Mathy Vanhoef and Frank Piessens released a warning on Monday about the KRACK security flaw, which allow hackers to hijack your Wi-Fi connection, inject content and monitor your traffic. Attackers could pluck your passwords out of thin air or redirect victims to websites packed with viruses.
Considering how Wi-Fi connections control almost everything we're on -- and Ethernet cables aren't exactly making a comeback -- the vulnerability has struck a nerve for even the most tech-averse people.
'Ideal targets'
While companies like Microsoft have already released patches for the vulnerability, IoT devices are much slower to update. This means the window of opportunity for hackers will last longer on your refrigerator than on your phone.
IoT devices are an "ideal target" for attacks based on the KRACK exploit because of slow patch times and insecure communication, said Ken Munro, a researcher and founder of security company Pen Test Partners.
If you visit an HTTPS website or use a virtual private network (VPN), your traffic will still be encrypted and hackers won't be able to steal anything from there. Luckily, more than half of the internet uses HTTPS, and "90 percent of the apps designed for phones and laptops" also use HTTPS, said Alexandru Balan, chief researcher at security company Bitdefender.
But when you use your phone to send commands to an IoT device, often times, it's unencrypted text, meaning anybody could see it if they're monitoring your traffic. Munro estimates that half of the IoT devices his company looked at use plain-text communication.
"All sorts of IoT devices do plain text communications -- virtually every class of device we've looked at from cars to CCTV to thermostats to cookers use plain text," Munro said.
For IoT devices, that's built in by design. Not all smart home devices need encrypted communication -- it's unlikely you'll need to enter a password to turn on a light bulb, for example. But consider your smart TV linked to your Netflix account or a smart refrigerator with access to your Amazon account.
Those devices hold sensitive information and are ideal targets for KRACK attacks.
"Most smart devices are designed for home use, and because of that, they don't necessarily require encryption for local traffic," Balan said. "Most smart TVs that I know of don't require authentication when you talk to them."
He sees a scenario where hackers can hijack what you're watching on a smart TV, while stealing information from it. And they'll likely be able to do it for months until the issue is patched -- if it's ever patched at all.
Patching the cracks
So far, only one mainstream IoT Wi-Fi module manufacturer has updated firmware to fix the vulnerability, Munro said. Espressif Systems, which provides Wi-Fi modules for IoT devices, said on Monday it released patches for KRACK.
Google and Amazon both said they're aware of the issue and will be sending patches in the coming weeks. This applies to all their devices, including the Google Home and the Amazon Echo , smart speakers that can control your home.
Nest Labs, a smart home vendor owned by Google parent company Alphabet, also said it's "rolling out patches to Nest products over the next couple weeks."
Communications on the Home and the Echo are encrypted in transit and at rest, unlike the majority of devices that IoT security researchers have seen. Nest's data is also encrypted, securing it from spies using KRACK's exploits.
The scrutiny on encryption stresses the importance of equipping your smart home from a reputable source, one that keeps security in mind and continues to update devices. The general advice has been to update your devices, but what happens if there isn't one?
Munro estimated that IoT devices and home routers "will be the most likely to stay unpatched and still be vulnerable in 6 to 12 months."
"So many IoT and related smart devices go out of support quickly, to be replaced by 'Smart Thing V2,'" Munro said. "So where's the incentive for vendors to continue supporting the old version?"
IoT devices that never get the necessary updates are sitting ducks to KRACK attacks.
The Smartest Stuff: Innovators are thinking up new ways to make you, and the things around you, smarter.
Tech Enabled: CNET chronicles tech's role in providing new kinds of accessibility.

