Security flaw could expose your encrypted emails, researchers warn
Researchers recommend you disable HTML rendering in your encrypted email clients to stop potential attacks.
The attack works by exploiting how email clients read HTML code, researchers said.
A security flaw with email encryption appears to have left a small opening for hackers to read your private messages.
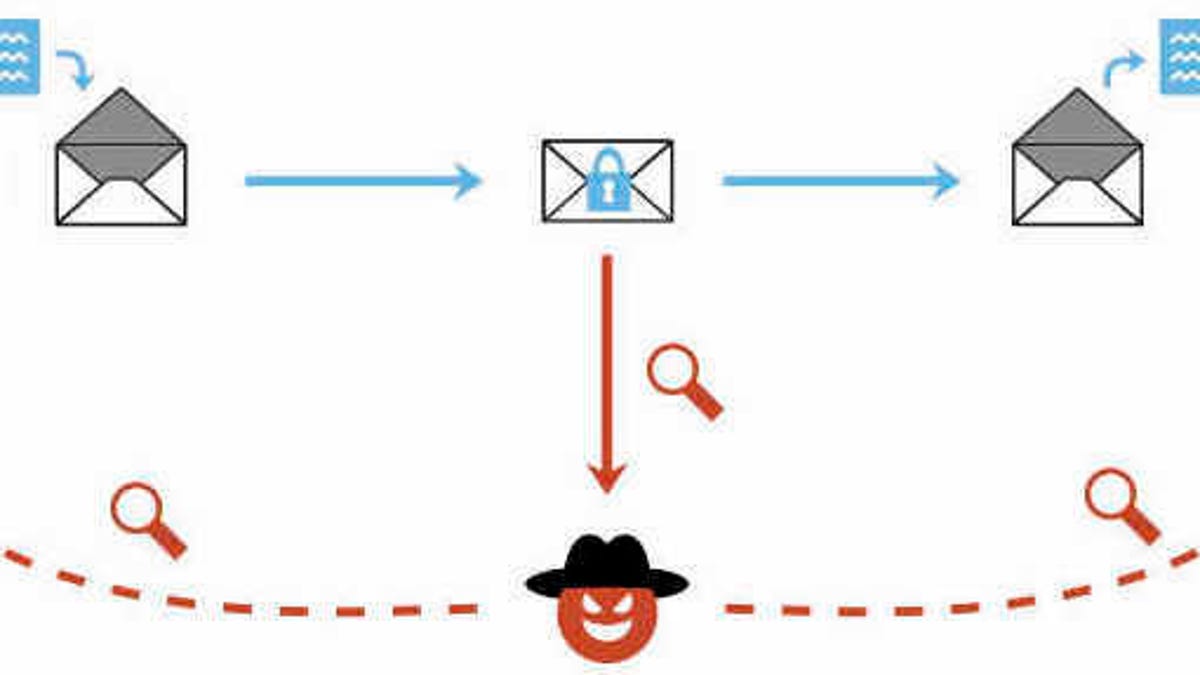
The vulnerability, which European researchers called Efail, doesn't break email encryption standards like Pretty Good Privacy (PGP), but takes advantage of a flaw from how email clients read HTML codes. While encrypted email keeps your messages secret, email clients see HTML content -- for example, images or hyperlinks -- and translate them in plain-text, even if there is encrypted content in them. The security flaw allows potential hackers to use that element to expose the most popular email encryption standards, the researchers said.
Sebastian Schinzel, the lead researcher on Efail and a professor of computer security at Münster University of Applied Sciences, said on Twitter that there were "currently no reliable fixes for the vulnerability."
The vulnerability requires several steps for an attacker to intercept encrypted emails, but reveals a crack in PGP's armor. The attacker would have to have access to the encrypted emails to begin with, meaning that the victim's account would need to be compromised as a starting point.
They then would have to send the contents of that encrypted email back to its owner -- the victim -- in a carefully crafted way to make email clients think it's HTML. This needs to be done in three emails, with the first one opening the HTML tag, the second one containing the encrypted message, and the third closing the HTML tag.
So clients like Apple Mail, iOS Mail and Mozilla Thunderbird would view the emails as HTML instead of an encrypted message, and display it as one plaintext email instead of three hashed messages.
"It's a lot of steps for sure, and one that honestly is more hypothetical than is it is dangerous," Dave Kennedy, the chief executive at security company TrustedSec, said.
The attack works for archived encrypted emails as well, not just recent messages.
The researchers recommend disabling HTML rendering in your email client to prevent your PGP messages from being decrypted. The Electronic Frontier Foundation has recommended that people temporarily stop using PGP email plugins, and use non-email based platforms like Signal for encrypted messages.
'Hello, humans': Google's Duplex could make Assistant the most lifelike AI yet.
Cambridge Analytica: Everything you need to know about Facebook's data mining scandal.

