Easy access to Airplane mode an iOS 7 security flaw -- researchers
A video posted to YouTube recently shows how the Control Center's Airplane mode in iOS 7 gives hackers the time they need to overcome a device's security functions.
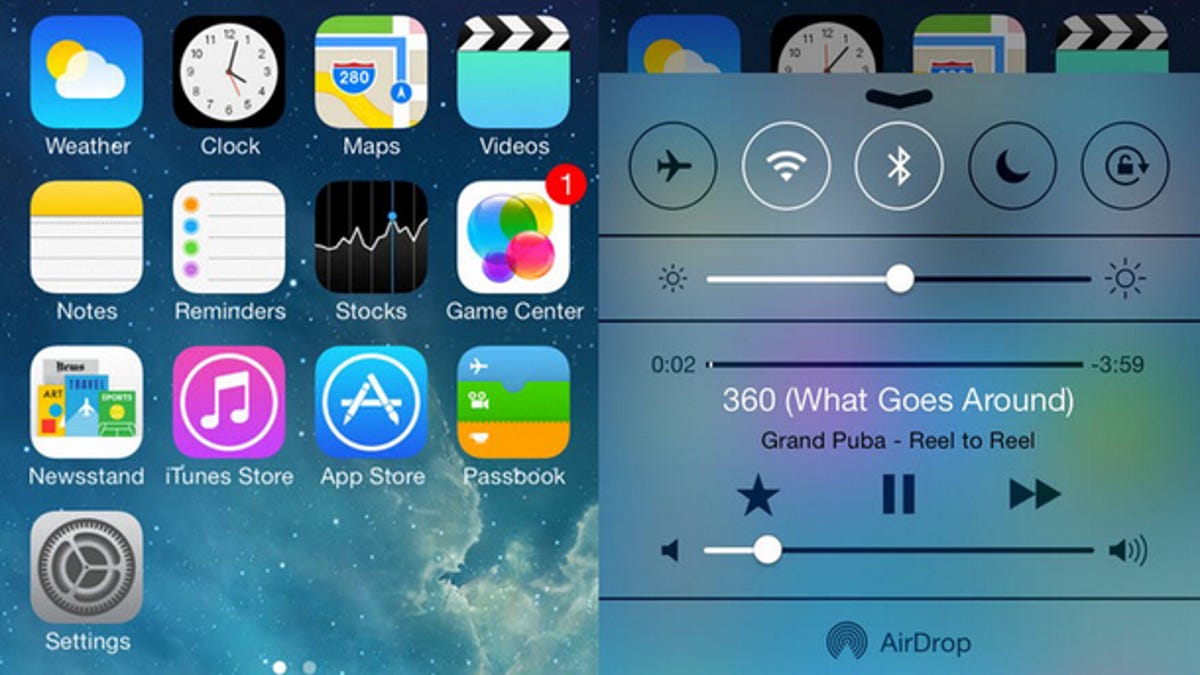
Apple's Control Center in iOS 7 makes it easier to access certain functions, but a recently released study from security researchers suggests it might be causing harm.
Security researchers at German firm SR Labs posted a video to YouTube recently showing how the easy access to Airplane Mode in Apple's Control Center could give hackers the extra time they need to exploit a device.
Here's how the scenario could play out: a hacker steals an iPhone running iOS 7. As soon as they get their hands on the locked device, they open Control Center from the lock screen and turn on Airplane Mode. From there, they set out to break into the device and change Apple ID passwords to prevent the owner from accessing the device.
The turning on of Airplane Mode is the important function in this scenario. Having easy access to Airplane Mode in iOS 7 effectively takes the device offline, eliminating the owner's ability to find out where the iOS device is and remotely wipe it. That provides hackers with the time they need to break into the device.
In iOS 6, Airplane Mode was available only after getting through the lock screen and there was no Control Center, meaning hackers couldn't take advantage of the hack in previous installations.
In addition, the researchers warned that Apple's Touch ID fingerprint sensor could allow for new attacks. In an interview with CNET sister site ZDNet, they indicated that creating a spoofed fingerprint to open the handset is as simple as snapping an image of a latent fingerprint with another device and using some equipment to complete the job. The researchers claim the fingerprint spoofing will only take one hour to complete.
Here's the full video to find out about iOS 7 and iPhone 5S flaws:

