I play the security odds in Las Vegas by rolling the Wi-Fi dice
Who hacks the hackers? An inside look at hunting for insecure connections at the largest cybersecurity gathering in the world.
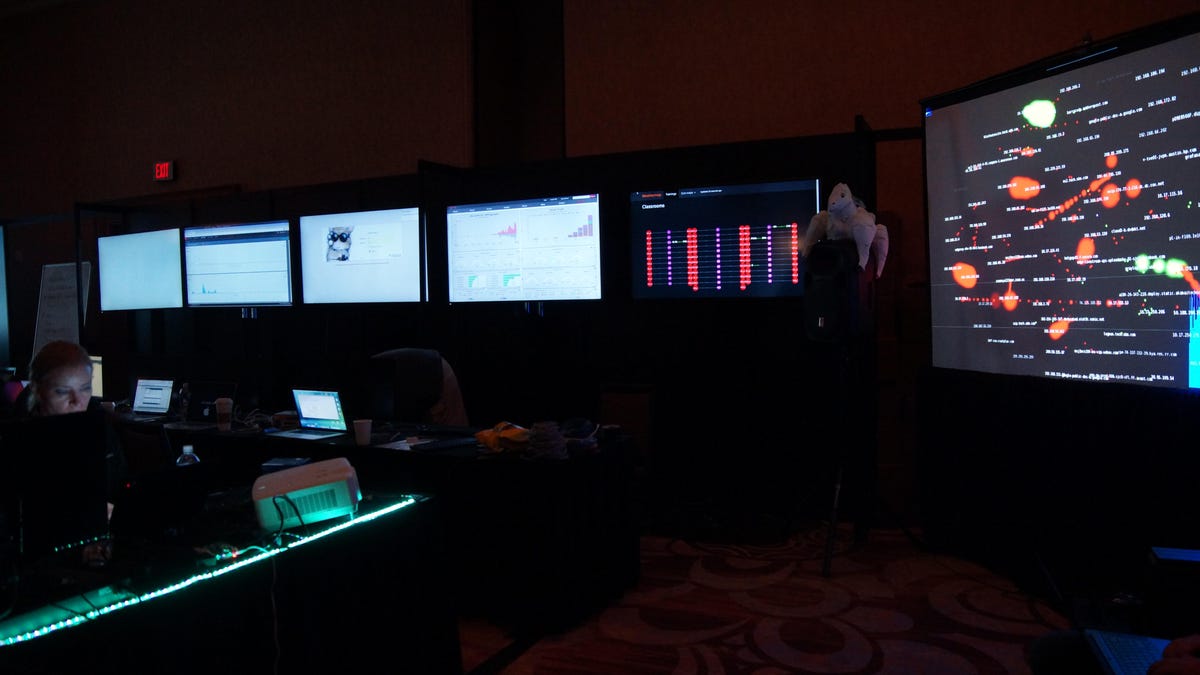
Inside the Network Operations Center at Black Hat, where a team of volunteers were working to protect the Wi-Fi from hackers.
It's worse than the Wall of Shame. It's the Wall of Sheep.
You're going to get hacked at Black Hat or Defcon, two of the largest hacker conventions in the world, if your device is insecure. And every year, hackers, security researchers and incognito federal agents attending the events, which run back to back, turn Las Vegas into a petri dish of cyberattacks. No phone, laptop or ATM is safe.
If you get hacked, you end up on the Wall of Sheep.
The wall is a massive shame list projected inside the Packet Hacking Village at Caesar's Palace during Defcon. Each year, hundreds of names are displayed though the organizers redact email addresses and passwords to protect the victims' privacy.
Being called a sheep means you didn't take enough care or simply didn't see a hack coming.
Thankfully, the hackers aren't after your identity or your money or anything else that could do you real harm. But they don't mind publicly shaming you into being more thoughtful about your security. Think of them as thoughtful burglars who enter your home to tell you your security system doesn't work.
"Riverside," one of the Wall of Sheep's co-founders, said it was easy to get thousands of logins and passwords within a minute when the presentation started more than 15 years ago. (Like many of the hackers at the conference, Riverside uses a pseudonym.) Now, people are much more careful.
"This has always been about security awareness for the flock," he said, during the second day of Defcon. He's expecting between at least 500 and 1,000 names to pop up on the wall by Defcon's end.
As a journalist, I should like my name to be everywhere. But I knew the Wall of Sheep was somewhere I didn't want to see my byline.
Sheep among wolves
The Wall of Sheep when it was kicking off at Defcon, with two dummy names on display.
"The Defcon network is considered the most hostile network in the world," Riverside said in an email. "As such, it's ever changing, making it difficult to teach specific techniques with consistent results."
Sheep usually get caught when their devices are connected to a compromised or public Wi-Fi network. Hackers sometimes create fake networks, like "WifiExtender," in order to trick people into connecting their devices. Once they respond to a few emails or tweets, their devices begin sending passwords and login information to the hackers.
And the victims' names end up plastered on the board.
To avoid getting hacked, I followed the digital hygiene regimen that experts advise. For example, if I want to go online, I use a wired connection. If I must go wireless, I use a cell connection through my phone or a hotspot.
When I'm surfing the web, experts say I should use a virtual private network, which routes all your information through secure computers. It's also good to use multi-factor authentication, meaning I get sent a password by text or a special code in an app to be able to log in.
Rolling the Wi-Fi dice
I got an offer from Lookout, a mobile security company, to test their new feature called Safe Wi-Fi, which is supposed to protect my devices from attacks over public Wi-Fi. What better place to test it?
Lookout's app feature "Safe Wi-Fi" told me DefCon-Open was safe, even though it's what the Wall of Sheep's packet hackers were using to lure unsuspecting sheep.
It's Las Vegas, time to roll the dice.
After connecting to the Wi-Fi on a dummy phone -- Did you think I'd be crazy enough to use my own device? -- Lookout's app began analyzing my connection, looking for the telltale signs of a hijacked network.
The Wi-Fi from my hotel room was safe, the app said, so I decided to start pressing my luck. I went to Defcon and began connecting to suspicious networks, like one called DefCon-Open. When I stopped by the Wall of Sheep, which was set up in a dark room with electronic music blasting and laptops galore, a hacker told me DefCon-Open was designed to catch clueless victims. Several names had already been put on the board.
Lookout's app told me DefCon-Open's network was "safe" though the Wall of Sheep hackers disagreed. Lookout says the version of its app that I was using only looked for fake networks, not people spying on the network, so it considered DefCon-Open safe. In other words, Safe Wi-Fi can tell you if you're on a compromised network but it can't stop hacks from happening.
My phone never appeared on the wall, but that's likely because I didn't use it to log into anything, the organizers said.
"Hack the hackers"
Not all the hackers at Defcon and Black Hat are as benevolent as the Wall of Sheep organizers. Fortunately, the conferences are prepared for them too.
There's an entire network operations center at Black Hat, where the convention's security teams are working around the clock to keep people safe.
The volunteers, backed with resources from RSA Security, Gigamon, Palo Alto Networks, Pwnie Express and other companies, watch over the countless networks at Black Hat. What they're looking for is anything weird.
The NOC, as it's called, is a dark room only lit by screens and a spotlight that looks like Batman's Bat signal on the wall. It's a silhouette of a man in a trenchcoat and a black hat, the conference's official symbol.
In one corner is a goofy but terrifying device called a Wi-Fi cactus, that looks like a glowing tree with spiky antennas coming out. Theoretically, it can scan for thousands of connections, but these hackers mostly use it as an amusing prop.
Neil Wyler, better know as "Grifter," helps run the center. He's in charge of making sure everything runs smoothly. With about 16,000 people attending Black Hat this year, it's definitely been a challenge.
Wyler, who works for RSA but was volunteering at the NOC, says the first day of Black Hat briefings was the toughest of the week.
"We have people who come onsite who are specifically looking to hack the hackers," Wyler said.
The first attack attempt came in just four minutes after Black Hat had opened. Wyler's team also found several home-made hacking devices hidden around the convention center.
By the end of Black Hat, the team had tracked half a million devices connecting to conference's wireless network. There were more than 300,000 visits to unsafe websites during Black Hat, Wyler said.
Some of the more inventive hackers attached wireless hotspots to drones that they flew within range of the conference, according to RSA Security. Grifter and his team found 10 such drones.
One of several scanners Pwnie Express had around the convention floor during Black Hat.
Pwnie Express, another company helping protect Black Hat's network, set up sensors around the convention, to monitor for any malware on incoming traffic. If there was any, Aaron Kless, the company's director of project management, said Pwnie Express could shut down the attacker remotely.
Surprisingly, both Kless and Grifter opted not to use the Wi-Fi they were tasked with protecting. That's because they find cellular networks to be more secure.
"The barrier to hacking 4G is much higher," Grifter said, referring to cellular data connections.
So I stuck to his advice and stayed on my cellular connection as well, despite its slower speeds. It's a small sacrifice for security.
Thankfully, I managed to leave Las Vegas without being labeled a sheep.

