McAfee software lets scammers hijack PCs to send spam
Computers running McAfee service are found to be acting as open proxies for spammers, customers report.
McAfee is looking into a problem with a service in its SaaS Endpoint Protection software that appears to be allowing computers to serve as open proxies for sending spam, the company told CNET today.
"We are aware of the issue and have both threat analytics and development teams diligently analyzing the problem and possible solutions," the company said in a statement. "We will have more information on the issue shortly."
A public relations representative said she was attempting to get more information on the matter but did not get back to CNET by the end of the work day. The problem was reported by McAfee customers on the Web who complained that their e-mails were being blocked by e-mail providers and their IP addresses were being blacklisted for sending spam.
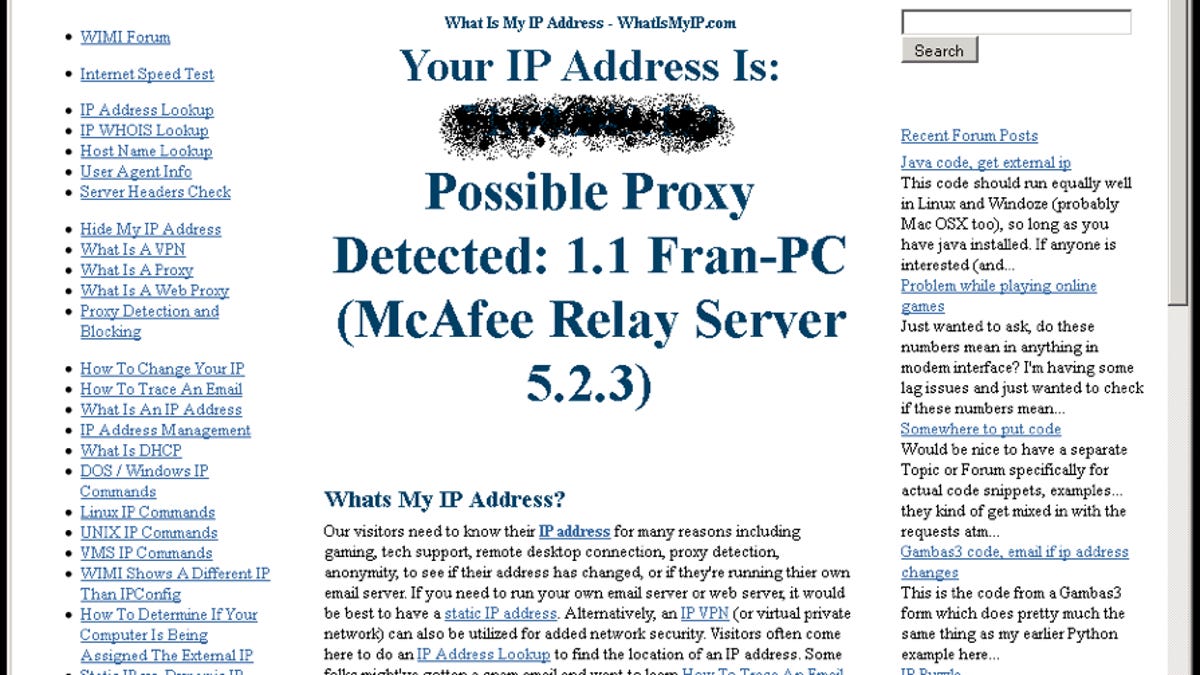
The problem appears to be in the RumorServer Service myAgtSvc.exe, McAfee Peer Distribution Service, which is part of McAfee SaaS Endpoint Protection Suite, previously known as Total Protection Service, according to the Kaamar Blog. The technology, used for delivering updates to computers without a direct Internet connection, serves as an Open Proxy on Port 6515, which effectively opens the computer up to being used by spammers to use the computer to send spam to other sites that looks like it is coming from that IP address, the blog post says.
The Kaamar blog first detected a problem on January 4 when e-mail was returned undelivered with a message saying "Our system has detected an unusual rate of unsolicited mail originating from your IP address."
"Our Windows 2008 server was one of the computers affected. We first realised there was a problem on the 4th January 2012 when an email was returned undelivered with the message: "Our system has detected an unusual rate of unsolicited mail originating from your IP address. To protect our users from spam, mail sent from your IP address has been blocked," the blog post says. "On checking through our mail logs, we also noticed that an earlier email sent 2nd January had been delayed with a message saying our IP was on the spamhaus/cbl list as being infected with a trojan spambot."
The Kaamar blog site was able to stop the traffic on January 5 but received a data limit warning from the ISP that the site was nearing its monthly limit for traffic in only a few days. The problem, which appeared to start December 31, 2011, caused the site to get the equivalent of 10 months of normal traffic in just one day, according to the post. Meanwhile, IP addresses for the site were on several public blacklists for spamming activity.
Mr.HinkyDink's UT Blog reported finding nearly 1,900 IP addresses serving as open proxies running the McAfee software since December 1, 2011.
The Kaamar blog has instructions for checking to see if a computer is affected and protecting computers until McAfee fixes the problem.
In the meantime, a McAfee customer posted on a Microsoft Technet forum that "McAfee has developed a patch that will instruct rumor to not respond to most incoming requests on port 6515. The patch will be posted through updates over a week time. The updated version will show 5.2.3 patch 4."
Update 8:59 a.m. PT January 18: A McAfee public relations representative said "this only affects SaaS, and a patch is forthcoming as soon as it clears testing," which is expected this week.

