Ransomware gang posed as real company to recruit workers
Group's professional-looking website advertised open positions for jobs to help it continue its criminal activities, researchers say.
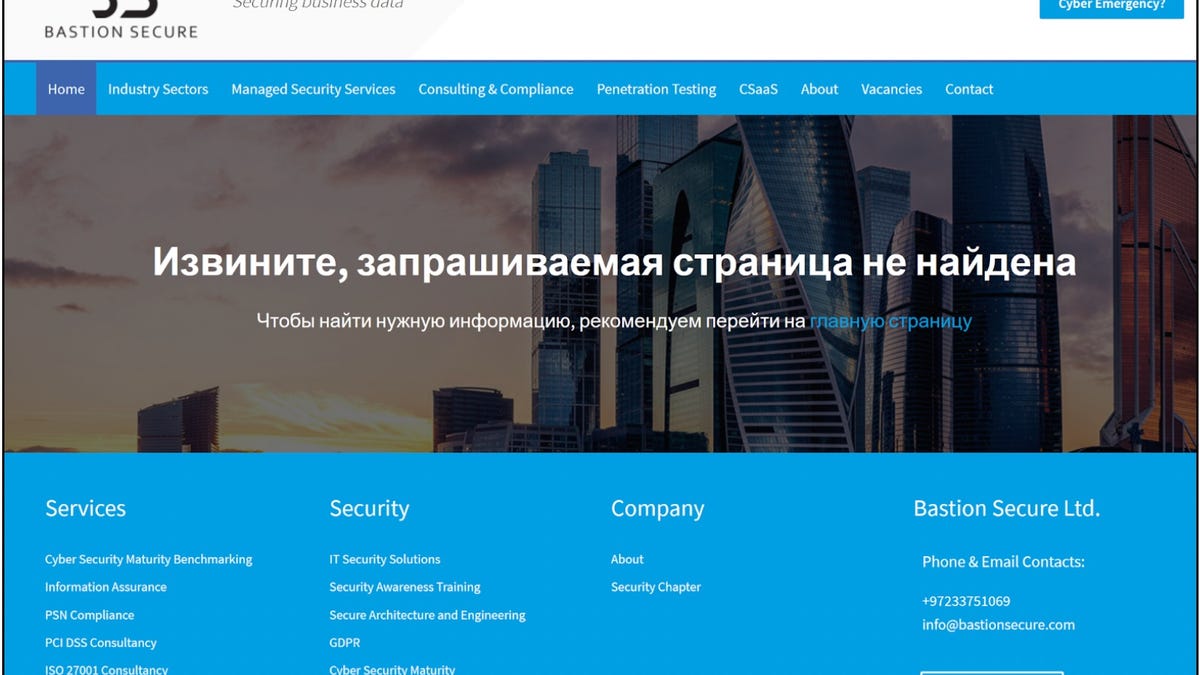
A screen shot of Bastion Secure's website, which has since been taken down.
A well-known Russian ransomware group set up a fake company to recruit technology workers to expand its criminal enterprise, security researchers say.
The fake company was created by Fin7, thought to have created the malware that crippled one of the largest fuel pipelines in the US in May, according to a new report by security firm Recorded Future's Gemini Advisory unit. The ruse, reported earlier by the Wall Street Journal, included a professional-looking website claiming the company offered cybersecurity services.
Fin7 has been linked to hacks targeting hundreds of companies worldwide, targeting point-of-sale systems used by major retailers. The threat group is also believed to be have developed the software behind the Colonial Pipeline hack that temporarily closed pipeline operations and disrupted gasoline delivery to parts of the Southeast earlier this year.
The group created a fake company called Bastion Secure, as well as a companion website that advertised open positions for programmers, system administrators and reverse engineers to assemble a crew capable of conducting tasks to support cybercriminal activity, the researchers said. Fin7 has a history of masquerading as real companies, leading researchers to believe that the group "is using the fictitious company Bastion Secure to recruit unwitting IT specialists into participating in ransomware attacks."
The group's recruitment effort was driven by "desire for comparatively cheap, skilled labor," the report states, offering starting salaries between $800 and $1,200 per month. While that would be a reasonable starting salary for an IT job in some Eastern European countries, it would be a "small fraction" of the group's profits from cybercrimes.
In investigating Bastion Secure, a Gemini source applied for a job at the fake company. While the first two stages included assignments IT specialists could typically expect in the interview process, in the third stage "it became immediately clear the company was involved in criminal activity," researchers wrote.
"The fact that the Bastion Secure representatives were particularly interested in file systems and backups signals that FIN7 was more interested in conducting ransomware attacks than POS [point of sale] infections," they wrote.
Gemini said that Fin7's desire to recruit unwitting accomplices was likely driven by greed.
"With willing accomplices, FIN7 would be forced to share a percentage of ransom payments totaling millions of dollars, whereas unwitting "employees" would work for monthly salaries in the low thousands, which are commensurate with the labor markets in post-Soviet states," researchers wrote.
Fin7 has been active since at least 2014 and is considered one of the largest cybercrime operations, attacking more than more than 100 US companies, with a focus on hotels, gaming establishments and restaurants, including attacks on Chipotle, Chili's and Arby's, according to the Justice Department.
Ransomware payments reached more than $400 million globally in 2020 and topped $81 million in the first quarter of 2021, the US government reported earlier this month.

