Yahoo password breach shows we're all really lazy
<b>commentary</b> It's time for companies to use basic security practices, and for individuals to use common sense with passwords.
I'm going to say it. Lame! That's what this Yahoo password leak is. Really, Yahoo? Shame!
A group of hackers say they used a common attack, known as SQL injection, to grab 450,000 passwords from a Yahoo database, and they released them to the Web last night. The passwords were stored in plain text and not obscured using a hashing technique, which is standard practice for companies that handle sensitive user data.
I've asked Yahoo to comment on why the company didn't hash the passwords, but so far it's only released a statement confirming that an older file from the Yahoo Contributor Network was broken into and that less than 5 percent of the Yahoo accounts on there had valid passwords. "At Yahoo we take security very seriously and invest heavily in protective measures to ensure the security of our users and their data across all our products," the statement says, without irony.
If the people at Yahoo really take security seriously, they should have protected against an SQL injection attack in the first place and hashed the passwords. At least LinkedIn had the decency to hash -- LinkedIn, eHarmony, and Last.fm had passwords leaked last month. And Formspring, whose passwords were stolen and posted to the Web a few days ago, took the extra step of salting them. "These hashes (on Formspring passwords) are 200 times harder to crack than passwords stolen from eHarmony or LinkedIn," because of the salting, Mike Kelly, a security analyst at Trustwave SpiderLabs, told me yesterday.
Yahoo and the others might want to, strike that, should consider using two-factor authentication for log-ins, like Google and Facebook offer. Basically, what this means is that someone who gets access to your username and password can't just use that information to log into your account. It works by requiring the user when logging in from a new or unrecognized device to type in a code that's sent to the user's phone.
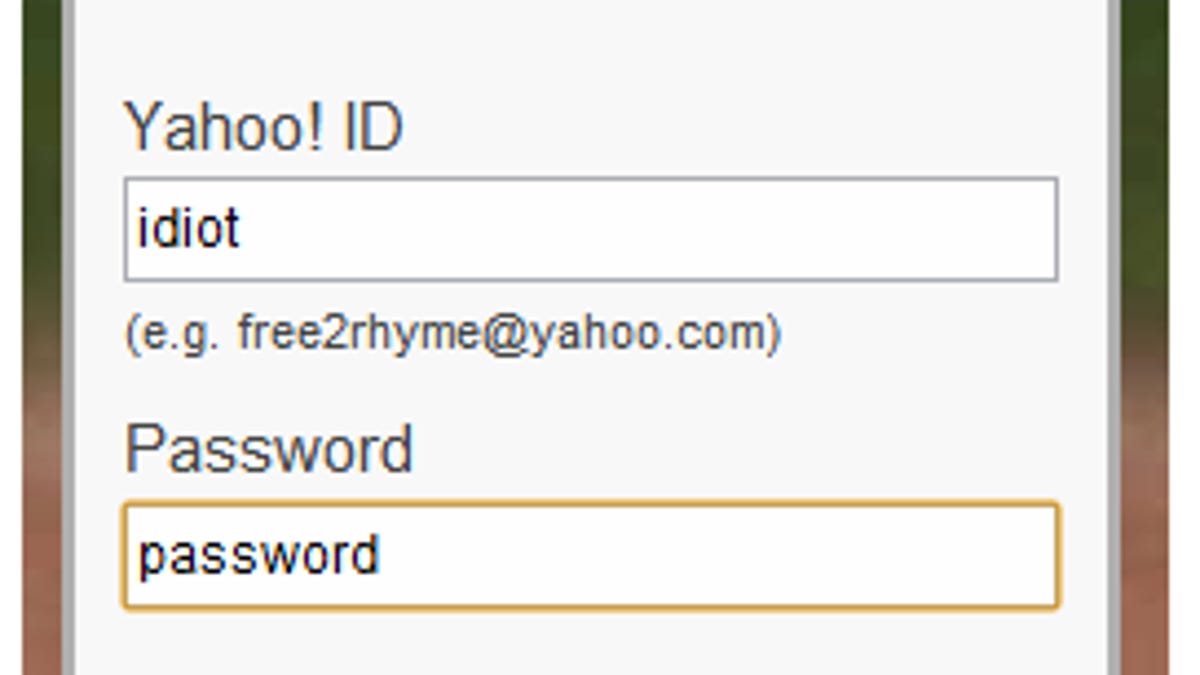
Yahoo also slipped up in not requiring stronger passwords on the Yahoo Contributor Network site. A CNET analysis of the passwords found that more than 2,200 of them were "123456" and 780 of the passwords were just "password," showing a total lack of imagination and utter carelessness on the part of those users.
Yahoo requires stronger passwords on its other sites, so maybe when Yahoo acquired Associated Content in 2010 and rebranded it Yahoo Contributor Network it forgot to beef up password security. At a minimum, sites should force people to pick passwords of at least eight characters and include upper and lowercase letters, and numbers and symbols, said Nicholas Percoco, head of Trustwave's SpiderLabs. "But if the passwords are stored in the clear, even this would be meaningless," he said.I've been harsh on Yahoo, and indeed none of this would have happened if the database and the passwords had been secured better. But it's truly disturbing how so many people just don't seem to understand that "password" is not a good choice for a password. What are they thinking when they hear about all these breaches and hacks? It's likely that many of these passwords were re-used on other sites, as well, which is a big no-no. More information on how to choose a strong password is here, and there are tons of password managers and other tools to help people create strong passwords.
C'mon people! You wouldn't leave your house key sitting on your front porch, would you? It's time for everyone to use common sense and be more careful in picking and storing passwords. Otherwise, data breach stories will continue to dominate the headlines, and it's getting kind of old.

