Security researchers find flaws in chips used in hospitals, factories and stores
The vulnerabilities are packed in chips used for Bluetooth connections, and can allow for serious attacks.
The security flaws come from Bluetooth Low Energy chips embedded on Wi-Fi access points, researchers said.
Popular Wi-Fi access points used by businesses are open to two critical security flaws, researchers said Thursday.
Researchers at Armis Labs, a security company with a focus on internet of things devices, found in tests that a hacker could completely take over network access points using the vulnerabilities on Bluetooth Low Energy chips.
BLE is a different standard from Bluetooth. First introduced in 2011 as Bluetooth 4.0, it boasts a much longer battery life than its predecessor. Because of that longevity, BLE chips are more likely to be used in IoT devices and medical devices.
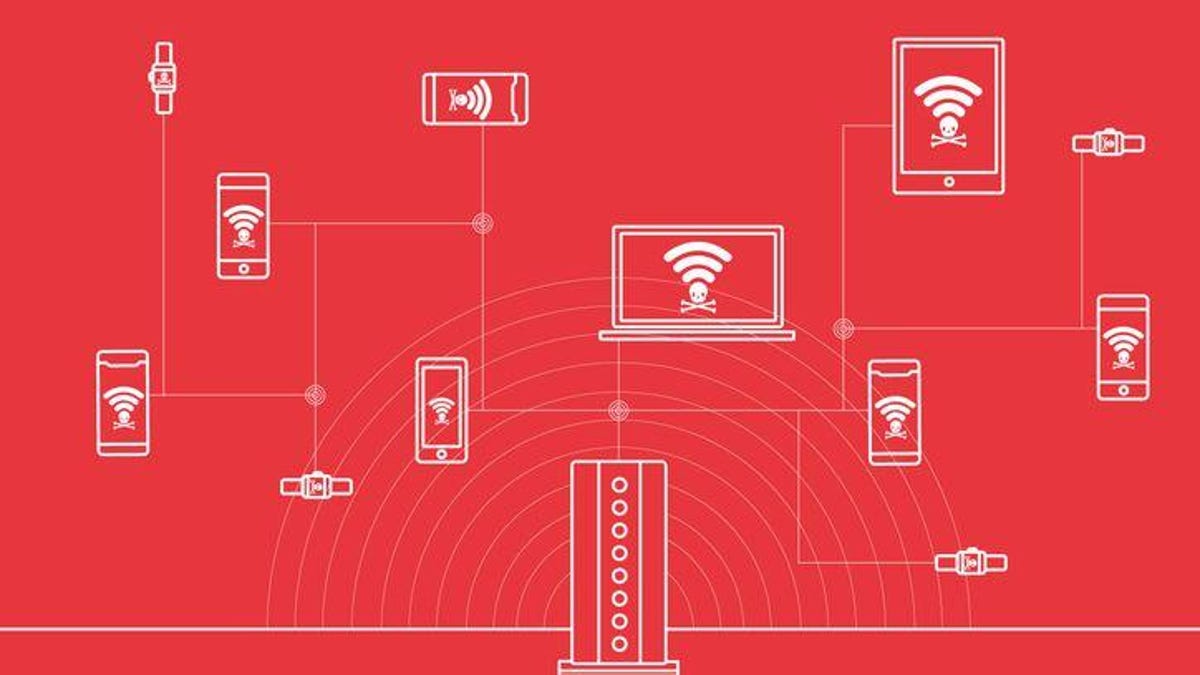
The BLE chip vulnerabilities -- researchers are labeling the pair of flaws "Bleeding Bit" -- would let attackers hijack vulnerable networks and spread malware to any devices connected to those networks, Armis Labs said. Though the hacker would have to be in the device's Bluetooth range, and the Wi-Fi access point would also need to be in scanning mode for the attack to work.
Wireless access points can come in many forms, such as a router or an internet of things device. If a hacker gains access to the network, it becomes much easier to attack devices connected to it. That's why the US and UK governments warned in April that Russian hackers were targeting millions of routers around the world.
These new vulnerabilities highlight the extent of possible openings an attacker has to infiltrate a network: While there may not be anything wrong with the wireless network itself, these hidden BLE chips provide a way in.
Many customers don't even know that the devices they bought are using these BLE chips, said Nadir Izrael, chief technology officer at Armis Labs.
"Most organizations don't even use any of those features, but they exist as an access point nonetheless," Izrael said.
The vulnerabilities
Armis Labs said the vulnerabilities are found in four BLE chips made by Texas Instruments, and are used in Wi-Fi access points from Cisco, Meraki and Aruba.
A security patch is expected for the flaws on Thursday, following Armis Labs' release of its research. Texas Instruments has already issued its patch. Cisco, which owns Meraki, has issued a security advisory for any customers potentially affected.
"We've informed Armis that the potential security vulnerability that they are exploiting was addressed with previous software updates. If our customers have not already updated their software with the latest versions available, we encourage them to do so," a Texas Instrument spokeswoman said in a statement.
"Fixed software is available for all affected Cisco products," a Cisco spokesperson said in a statement. "Cisco is not aware of any malicious use of the vulnerability."
Cisco also noted that the vulnerabilities are present only when certain conditions are met: when an attacker is near the device, when the BLE feature is enabled and when scanning mode on the device is enabled.
HP, which owns Aruba, did not respond to requests for comment.
The first vulnerability affects Cisco's and Meraki's Wi-Fi access points, and works by taking advantage of a flaw in how the BLE chips analyze incoming data, security researchers said.
Each time data is sent to the BLE chip, the traffic is supposed to have a field that's only six bits long. But these chips look at an extra two bits, and attackers can inject whatever values they want in those fields.
This is commonly known as a buffer overflow attack, where attackers send more data to a BLE chip than it's supposed to handle, causing memory corruption. That failure would give an attacker full control over the wireless access point, researchers said.
"It's very simple to produce, and it causes automatic memory corruption," said Ben Seri, Armis Labs' vice president of research.
The second vulnerability affects Aruba's Wi-Fi access point Series 300 and stems from an issue with Texas Instruments' firmware updates, Seri said. The BLE chips have a feature called Over Air Download, which allows for software upgrades. It's supposed to be only a development tool, and not in products available for sale.
This feature also has no security measures, which means attackers can install malware posing as updates on these devices, Izrael said.
"An attacker can just change the code to be his own malicious code and that can be used to access the network," he said.
Who's affected
Hospitals, offices, factories and stores use devices that rely on these chips, Armis Labs said.
The vulnerabilities impact industries across the board, including health care, automotive and retail. Affected devices aren't limited to just routers. Izrael said the chips are used in pacemakers and insulin pumps too.
For the first vulnerability, Armis Labs recommends updating your devices to the latest Texas Instruments version. For the second vulnerability, the researchers said to stop using Over Air Download, which is an optional feature.
"You don't want medical devices being hacked," Izrael said. "You don't want people getting access to a smart lock."
Security: Stay up-to-date on the latest in breaches, hacks, fixes and all those cybersecurity issues that keep you up at night.
Taking It to Extremes: Mix insane situations -- erupting volcanoes, nuclear meltdowns, 30-foot waves -- with everyday tech. Here's what happens.

