Malware went undiscovered for weeks on Google Play
Breaking the malware into separate, staged payloads allowed the Trojan's authors to avoid detection by Google's automated screening process.
Security researchers have discovered malware hosted on the Google Play marketplace that went weeks undetected masquerading as games.
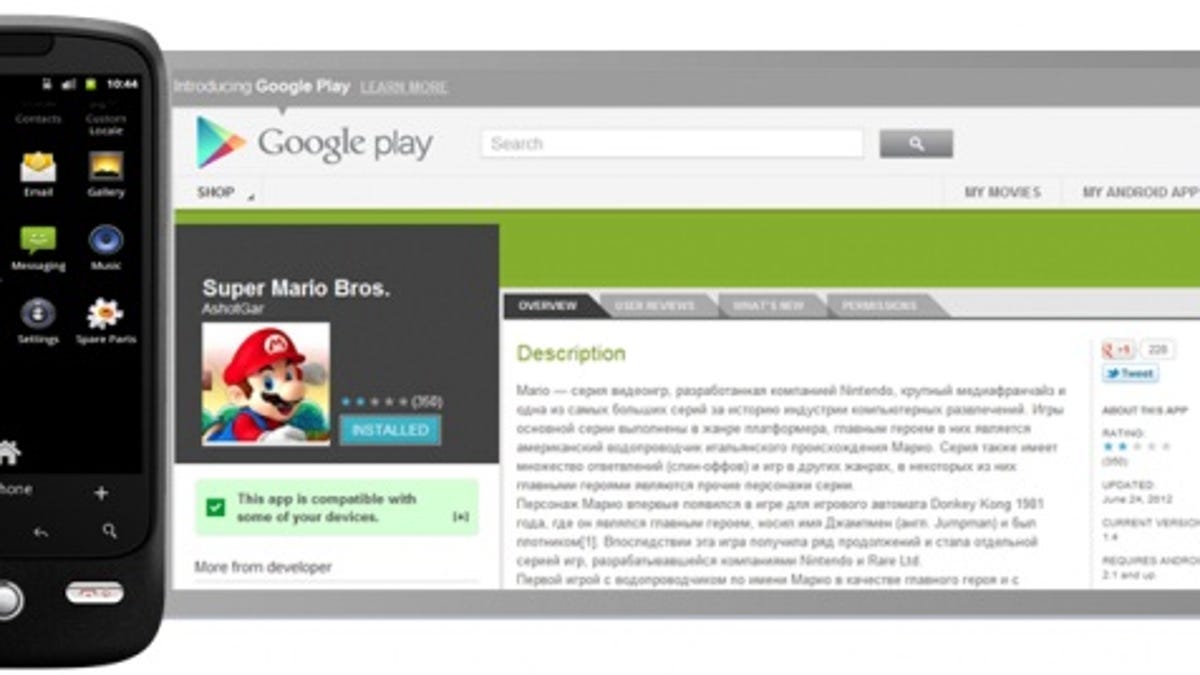
Android.Dropdialer, a Trojan that sends costly text messages to premium-rate phone numbers in Eastern Europe, had gone undiscovered for two weeks in the form of two game titles, Symantec researcher Irfan Asrar wrote in a blog post yesterday. The two games -- "Super Mario Bros." and "GTA 3 - Moscow city" -- were uploaded to Google Play on June 24 and generated 50,000 to 100,000 downloads, Asrar said.
"What is most interesting about this Trojan is the fact that the threat managed to stay on Google Play for such a long time, clocking up some serious download figures before being discovered," Asrar wrote. "Our suspicion is that this was probably due to the remote payload employed by this Trojan."
The Trojan's authors avoided detection during Google Play's automated screening process by breaking up the malware into separate, staged payloads, Asrar said. Once downloaded and installed from Google Play, the apps would download an additional package for installation that sent the text messages.
The discovery highlights another flaw in Google's Bouncer, an automated process introduced earlier this year that scans apps for known malware, spyware, and Trojans, and looks for suspicious behaviors and compares them against previously analyzed apps. If malicious code or behavior is detected, the app is flagged for manual confirmation that it is malware.
However, Duo Security's Jon Oberheide and Charlie Miller demonstrated in June how they exploited weaknesses in Bouncer to sneak malicious apps onto Google Play. Their technique allowed them to "fingerprint the Bouncer environment, allowing a malicious app to appear benign when run within Bouncer, and yet still perform malicious activities when run on a real user's device," Oberheide said at the time.
CNET has contacted Google for comment and will update this report when we lean more.

