New malware roosting place: Inside your SD Card?
A pair of security researchers have figured out how to subvert tiny controller chips in flash-memory storage devices, an approach that could expose people's private data.
Security researchers have found a way to hack SD Cards, the most common form of flash-memory cards used to store data mobile phones and digital cameras, and run software that intercepts data.
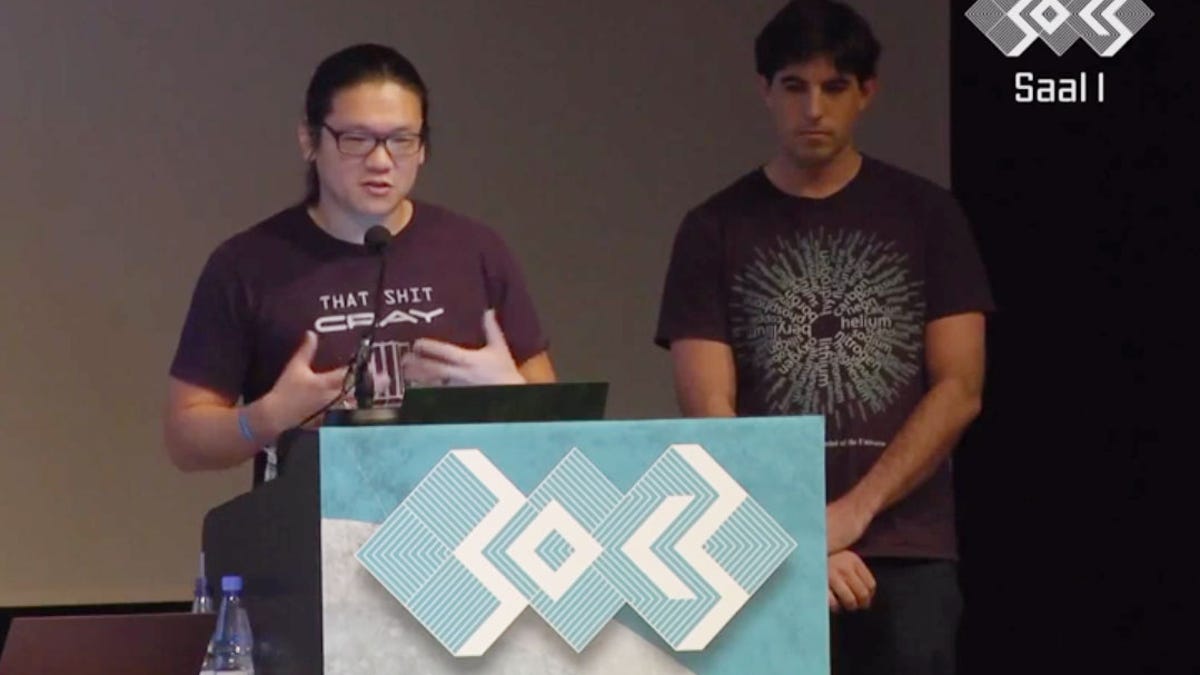
Andrew "bunnie" Huang and Sean "xobs" Cross disclosed the approach Sunday in a blog post and talk at the Chaos Computer Congress (30C3). With the attack, a person could run malicious software on the memory card itself. That's because the cards have tiny built-in computers called microcontrollers that are used to oversee the details of data storage.
The result is a "perfect setup for a man-in-the middle attack," Huang said in a video of the talk. The current approach to flash-memory storage has "invited someone to go sit in between our data, and we just trust them to do whatever they want to do."
In a man-in-the-middle attack, someone intercepts data that's being transferred from one location to another, potentially scrutinizing or modifying it. Huang and Cross believe their attack could be used to secretly copy data, to modify sensitive data such as encryption keys, or to subvert authentication processes by substituting an unauthorized file for execution instead of the actual file that was authorized.
The approach works in principle not just with SD Cards, where the researchers demonstrated their approach, but also with other flash-memory devices such as SSDs (solid-state drives) used in place of traditional hard drives in personal computers and eMMC (Embedded Multimedia Controller) storage used in mobile phones.
To get the approach to work, the researchers had to reverse-engineer proprietary workings of the controller chips. First they figured out how to get a microcontroller to accept and then run new firmware -- a tiny operating system, in effect. Then they figured out the chips' actual proprietary commands.
The specific vulnerability Huang and Cross describe doesn't apply to all flash-memory devices because it's dependent on the specific microcontroller used. However, they believe the approach is generally effective since all flash devices rely on such controllers to figure out how to work around bad memory cells in flash-memory systems.
Cross and Huang also point out a little upside of the work: The hardware hacker community now has access to microcontrollers that are much cheaper than typical hardware such as Arduino systems. The input-output speeds of an SD Card might not be fast enough for many purposes, but they could be handy for data logging on Net-connected sensors, for example.
"An Arduino, with its 8-bit 16 MHz microcontroller, will set you back around $20," Huang wrote. "A Micro-SD card with several gigabytes of memory and a microcontroller with several times the performance could be purchased for a fraction of the price."

