Microsoft's Web map exposes phone, PC locations
Microsoft collects and publishes the locations of laptops, phones, and other Wi-Fi devices without taking the privacy precautions that Google and Skyhook Wireless have, CNET has learned.
Microsoft has collected the locations of millions of laptops, cell phones, and other Wi-Fi devices around the world and makes them available on the Web without taking the privacy precautions that competitors have, CNET has learned.
The vast database available through Live.com publishes the precise geographical location, which can point to a street address and sometimes even a corner of a building, of Android phones, Apple devices, and other Wi-Fi enabled gadgets.
Unlike Google and Skyhook Wireless, which have compiled similar lists of these unique Wi-Fi addresses, Microsoft has not taken any measures to curb access to its database. Google tightened controls last month in response to a June 15 CNET article, and Skyhook uses a limited form of geolocation to protect privacy.
Microsoft assembled the database through crowdsourced data gathering from Windows Phone 7 devices and through what it calls "managed driving" by Street View-like vehicles that record Wi-Fi signals accessible from public roads. Its Web interface is, the company says, intended to provide "search results, weather, movie times, maps and directions based on a device's current location."
CNET has confirmed how Live.com's interface works independently and also with Elie Bursztein, a postdoctoral researcher at the Stanford Security Laboratory who recently analyzed Microsoft's application programming interface, or API. He plans to summarize his findings in a related talk with two other researchers at the Black Hat security conference in Las Vegas next week.
Bursztein recommended that Microsoft adopt some of the same limits that its competitors already have. "I think what Google does is the smart thing to do," he said. "It's a pretty good solution."
Reid Kuhn, a program manger with Microsoft's Windows Phone Engineering Team, sent CNET this statement: "To provide location-based services, Microsoft collects publicly broadcast cell tower IDs and MAC addresses of Wi-Fi access points via both user devices and managed driving. If a user chooses to use their smartphone or mobile device as a Wi-Fi access point, their MAC address may also be included as a part of our service. However, since mobile devices typically move from one place to another they are not helpful in providing location. Once we determine that a device is not in a fixed location, we remove it from our list of active MAC addresses."
Microsoft did not, however, respond to questions whether its database includes only Wi-Fi devices acting as access points, or whether client devices using the networks have been swept in as well--something that Google did with its Street View cars. A May blog post touts "Transparency About Microsoft's Practices," but doesn't provide details.
If Microsoft collects and publishes only the Wi-Fi addresses of access points, the privacy concerns are lessened. But millions of phones and computers are used as access points--tethering is one example, and the feature is built into Apple's OS X operating system--meaning that their locations could be monitored.
It's true that Wi-Fi addresses, also called MAC addresses, aren't typically transmitted over the Internet. But anyone within Wi-Fi range can record yours, and it's easy to narrow down which addresses correspond to which manufacturer.
Someone, such as a suspicious spouse, who can navigate to the About screen on an iPhone or a laptop's configuration menu can obtain it in a few seconds as well. And hobbyist hacker Samy Kamkar created a proof-of-concept code last year that uses what's known as a cross-site scripting attack to grab the location of Wi-Fi routers that can be seen from an unsuspecting visitor's computer.
Geolocation privacy time line
Here's how the debate over privacy and geolocation, which allows wireless devices to speed up location fixes, has evolved:
April 2011: Apple iPhones and Android devices not only transmit location data, but also store it
April 2011: Windows Phone 7 devices also collect records of users' physical locations of customers and transmit them to Microsoft
April 2011: Apple says it will fix iPhone tracking "bug"
June 2011: CNET reports that Google publishes the estimated location of millions of phones, laptops, and other Wi-Fi devices
June 2011: Google curbs Web service that exposed the locations of phones, laptops, and other Wi-Fi devices
July 2011: Confirmation that Google's Street View cars collected the locations of not only Wi-Fi routers, but also devices using those wireless networks
A Microsoft representative pointed CNET to a list of Web pages, including one describing how geolocation works in Internet Explorer 9 and another discusses Windows Phone 7 and geolocation. Microsoft does not appear to provide an opt-out mechanism that would allow someone to remove his or her Wi-Fi address from the Live.com database.
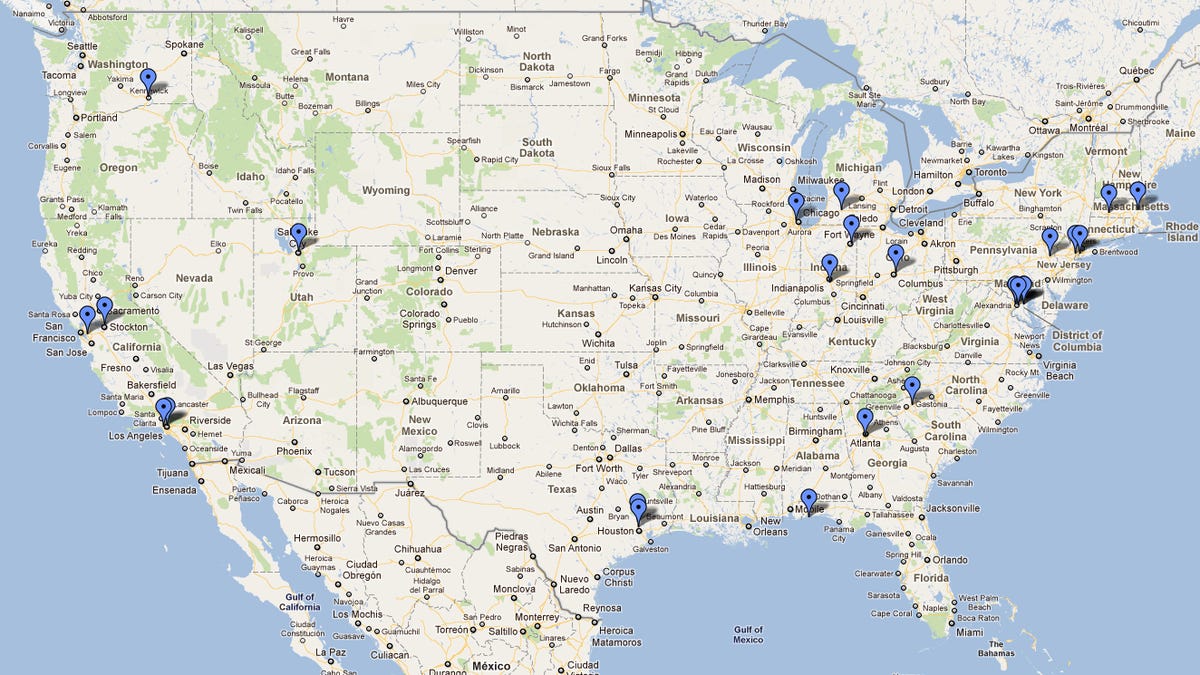
Microsoft's database extends beyond U.S. locations. A CNET test of a range of Wi-Fi addresses used by HTC devices showed that Live.com returned locations linked to street addresses in Leon, Spain; Westminster, London; a suburb of Tokyo, Japan; and Cologne, Germany.
Some Wi-Fi addresses appeared to change positions, meaning the Live.com database--located at http://inference.location.live.com--could be used to track the movements of a handheld device. In addition, some Wi-Fi addresses were added or deleted to the database over the period of a few days.
Google has taken multiple privacy steps that Microsoft has not, including using geolocation to filter requests (to find out where a wireless device is, you already have to know it's approximate location to about one city block). Another is that the search company's database does not appear to include the Wi-Fi addresses of Android devices acting as wireless hotspots.
Here's how it works: iPhone and Android devices automatically change their Wi-Fi MAC address when acting as an access point. Android devices appear to choose a MAC address beginning with 02:1A.
Google's database doesn't include the MAC address 02:1A:11:F2:12:FF. But Microsoft's does, and reports that it is located in the Embassy of Montenegro on New Hampshire Avenue in Washington, D.C.
Disclosure: McCullagh is married to a Google employee not involved in this issue.
Updated 11:05 a.m. PT: To include a statement from Microsoft.
Starting in April, CNET posed a series of questions to Microsoft that have gone unanswered. We also asked Apple and Google similar questions. Here's an abbreviated list:
June:
- Do you collect the MAC addresses of client devices or just access points? (The identification of an AP is reported in the BSSID field of the WiFi header.)
- Do you collect the MAC address of mobile devices including laptops that are acting as APs?
- What privacy policy governs this?
- What mechanism do you provide to let people opt-out if they don't want Microsoft to track the location of their device?
- Have you received any civil subpoenas, requests from law enforcement, or any other form of compulsory process for access to geolocation data based on MAC address?
- Do you make this location database publicly accessible via an API or other mechanism?July:
- How many entries are in this database?
- How frequently is it updated?
- How many entries are client MAC addresses?
- Why do you not take steps similar to Google and Skyhook to restrict access to it?
- Does Microsoft currently collect or has it ever collected client MAC addresses through any mechanism, including Windows Phone 7 crowdsourcing or "managed driving?"April:
- When did Microsoft start collecting location data from mobile devices?
- How frequently do devices running Windows Phone 7 transmit the data to Microsoft? Every 15 minutes? Hourly? Daily?
- Is the connection encrypted? If so, using what method?
- What information, exactly, is transmitted?
- You say the information collected includes a "randomly generated unique device ID." Is that device ID ever changed? If it is changed, how often does it change?
- You say the randomly generated ID is "retained for a limited period." How long is that? Is the ID then deleted or only partially anonymized?
- Given a street address or pair of GPS coordinates, is Microsoft able to produce the location logs associated with that generated ID, if legally required to do so?
- Given a generated ID, is Microsoft able to produce the complete location logs associated with it, if legally required to do so?
- Given a MAC address of an access point, is Microsoft able to produce the generated IDs and location data associated with it, if legally required to do so?
- How many law enforcement requests or forms of compulsory process have you received for access to any portion of this database?
- If Microsoft knows that a Hotmail user is connecting from a home network IP address every evening, it would be trivial to link that with an Windows phone's device ID that also connects via that IP address. Does Microsoft do that?