Mahdi 'Messiah' malware targeted Israel, Iran PCs
Trojan with references to Islam, Farsi language, and Israel-Iran conflict is found on hundreds of PCs in the Middle East.
A data-stealing Trojan capable of recording keystrokes, screenshots and audio and stealing text and image files has infected about 800 computers, mostly in Iran and Israel, over the last eight months, researchers said today.
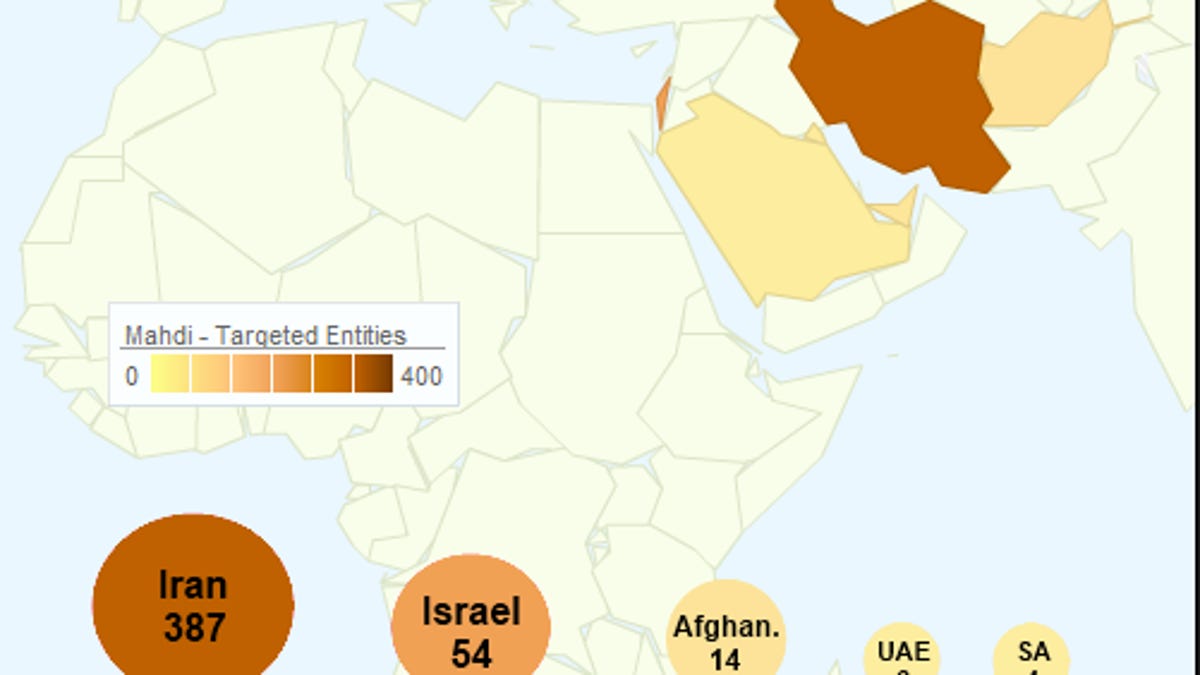
The malware, dubbed "Mahdi" (also "Madi") because of references in the code to the word for the Islamic Messiah, included strings in Farsi and dates in the Persian calendar format in communications with a command-and-control server in at least one of the variants, and a server that was located in Iran for at least one campaign, according to a blog post from Israel-based security firm Seculert. The victims included critical infrastructure companies, government embassies, financial services firms in Iran, Israel, Afghanistan, UAE, Saudi Arabia and other Middle Eastern countries, as well as the U.S. and New Zealand, Symantec reported.
Despite the types of victims and countries affected, the researchers said it was unclear whether it was a state-sponsored attack or not.
The campaigns started out with social engineering via an e-mail attachment. In one campaign, the attached file executed a malware dropper that contained a Word document of a news article with the headline "Israel's Secret Iran Attack Plan: Electronic Warfare," Seculert said.
Other targets featured malicious PowerPoint attachments that displayed video stills showing a missile destroying a jet plane and a dialog box asking for permission to run an executable .scr file, according to Symantec researchers, who found a command-and-control server in Azerbaijan, while Seculert found some in Canada, as well.An "Activated Content" PowerPoint feature enables executable content within the spearphishing attachments to be run automatically and the embedded downloaders install backdoor services on the system, according to a Kaspersky blog post. One example delivered the executable within a confusing math puzzle slideshow, while another showed a series of religious, nature-themed images with messages in English and poor Hebrew. Kaspersky also saw images displayed of a nuclear explosion and a video, which were likely designed to trick the victim into thinking nothing untoward was happening, Russia-based Kaspersky said.
This is just the latest piece of malware with links to Iran. Flame, Stuxnet and its cousin Duqu all targeted critical computer systems in Iran and neighboring countries. Flame and Stuxnet reportedly were developed by the U.S. and Israel.

