Google curbs Web map exposing phone locations
Google limits access to geolocation database linking Wi-Fi devices with physical locations after a CNET article highlights potential privacy concerns.
Google has taken steps to limit the disclosure of the locations of millions of iPhones, laptops, and other devices with Wi-Fi connections after a CNET article drew attention to privacy concerns.
The move by Google comes after the Mountain View, Calif.-based company was criticized for the way it made a database assembled by Android phones and Street View cars available to the public, even though it could link a geographical location with a unique hardware address of a Wi-Fi enabled device. The change means that Google now appears to be moving closer to the approach adopted by Apple and Microsoft, which never made their location databases public.
A source close to Google said some changes have been made to the way Google's location server processes location requests. A Google spokesman declined to comment.
Wi-Fi-enabled devices, including PCs, iPhones, iPads, and Android phones, transmit a unique hardware identifier, called a MAC address, to anyone within a radius of approximately 100 to 200 feet. Until CNET's June 15 article was published, if someone captured or already knew that unique address, Google's server could reveal a previous location where that device was located, including home or work addresses or even the addresses of restaurants frequented.
It wasn't immediately clear what changes Google made to provide more privacy protections, which could include not responding to some types of location requests or ones from certain geographical regions. The database is used to speed up geolocation fixes for mobile devices, and to provide the ability to determine location for PCs that don't have access to GPS-derived coordinates.
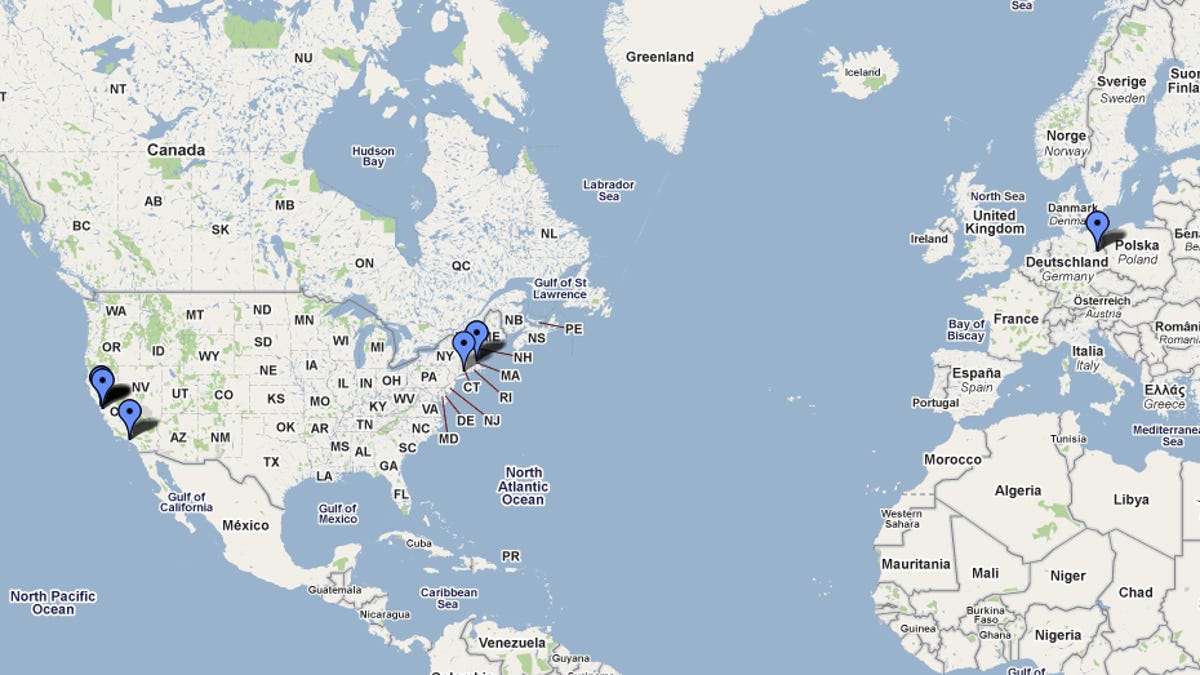
Out of approximately 3,000 MAC addresses that CNET tested over the last few days, not one delivered a location from Google's database. Before June 15, Google's database showed them as appearing in locations as varied as Satsuma, Ala., near Charing Cross station in London, Newport News, Va., outside of Beijing, China, and so on.
But Nick Doty, a lecturer at the University of California at Berkeley who co-teaches the Technology and Policy Lab, said Google's service appeared to be returning results when used in a browser instead of a Perl or Python script. "Maybe they're just trying to crack down on people using it for independent testing," said Doty, whose laptop had been linked in Google's database to his previous home in the Capitol Hill neighborhood in Seattle.
Approximately 10 percent of laptops and mobile phones using Wi-Fi appear to have previously been listed by Google as corresponding to street addresses. In an earlier statement, Google said: "We collect the publicly broadcast MAC addresses of Wi-Fi access points. If a user has enabled wireless tethering on a mobile device, that device becomes a Wi-Fi access point, so the MAC address of such an access point may also be included in the database. Wi-Fi access points that move frequently are not useful for our location database, and we take various steps to try to discard them."
A Google spokesman, however, declined to say that only access points appear in the company's location database. Alissa Cooper, chief computer scientist at the Center for Democracy and Technology and co-chair of an Internet Engineering Task Force on geolocation, says that her laptop was never used as a Wi-Fi access point. Her previous street address off of Connecticut Avenue in Washington, D.C., where she lived from 2007 to 2009, was nevertheless listed.
Getting a better handle on location-based data
Kim Cameron, Microsoft's chief identity architect until earlier this year, reached the same conclusion. In a June 2010 essay that analyzed an independent report (PDF) of Street View data collection, Cameron wrote that Google recorded the locations and MAC addresses of far more than just fixed Wi-Fi access points.
"There is no longer any question," he wrote. "The MAC addresses of all the Wi-Fi laptops and phones in the homes, businesses, enterprises and government buildings were recorded by the driveby mapping cars, as were the wireless access points, and this regardless of the use of encryption."
Google seems to be continuing to make changes to its location database. For an iPhone previously shown as being located in Brisbane, Australia, a Web interface to Google's location database created by hobbyist hacker Samy Kamkar recently returned a latitude of 0 and a longitude of 0 (west of Angloa in the Atlantic ocean). Last night, for the same Australian iPhone MAC address, the Web site yielded an error message instead.
Marc Rotenberg, head of the Electronic Privacy Information Center in Washington, D.C., compared Google's move to Apple's decision in April to fix what it called an iPhone "bug" that could record previous locations visited, which came as public interest in the topic began to rise.
"Even the companies don't fully understand how they're collecting location-based data," Rotenberg said. "That's one more reason why the emphasis in this area has to be on better practices, not better privacy policies."
Google's location database could previously be used, in a few cases, to track movements. One HTC device connecting to a San Francisco South of Market Wi-Fi hot spot moved from the BWI airport to a street address in an Atlanta suburb in one day. Another device that security researcher Ashkan Soltani spotted in a San Francisco coffeehouse moved from the engineering building of Ruhr-University in Bochum, Germany, across the main road to the university center.
An April 2010 statement (PDF) from Raphael Leiteritz, a Google product manager, says the location database is accessed by sending "a list of MAC addresses which are currently visible to the device." In response, Google compares those addresses "with its list of known MAC addresses," and then returns the "approximate location." Senate testimony (PDF) last month by Google public policy director Alan Davidson said: "A database of known network locations is required to determine a user's estimated location from either Wi-Fi access point or cell tower information."
To be sure, it's not always easy to learn a target's MAC address. It's generally not transmitted over the Internet. But anyone within Wi-Fi range can record it, and it's easy to narrow down which MAC addresses correspond to which manufacturer. Someone, such as a suspicious spouse, who can navigate to the About screen on an iPhone can obtain it that way too.
Disclosure: McCullagh is married to a Google employee not involved in this topic.