Drones can be hijacked via GPS spoofing attack
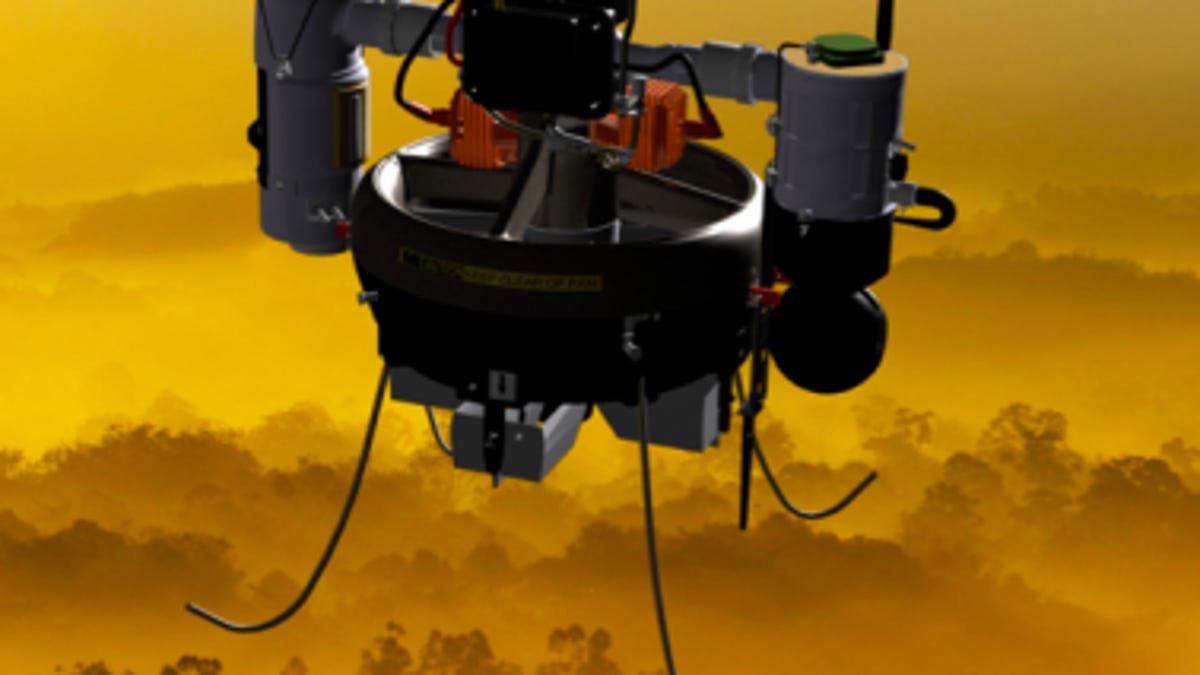
Researchers demonstrate how to remotely commandeer a drone in flight by tricking its GPS signals.
Last year a U.S. military drone doing reconnaissance in Iran disappeared. Iranian government officials there said they had steered the device off course by interfering with its GPS signals.
Such an attack, called GPS spoofing, had previously been considered theoretical. A research team at the University of Texas at Austin has demonstrated that the GPS signals of an unmanned aerial vehicle can be commandeered remotely. This demonstration highlights security concerns with plans to allow thousands of military and civilian drones in U.S. airspace by 2015.
"I think this demonstration should certainly raise some eyebrows and serve as a wake-up call of sorts as to how safe our critical infrastructure is from spoofing attacks," Milton R. Clary, a senior Department of Defense (DoD) Aviation Policy Analyst at Overlook Systems Technologies, said in the university's news release on the research released today.
The scenarios are worrisome. Drones could be re-routed to crash into people or buildings. Drones used in air strikes could be directed at other targets.
"We're raising the flag early on in this process so there is ample opportunity to improve the security of civilian drones from these attacks, as the government is committed to doing," said Todd Humphreys, assistant professor at the Cockrell School of Engineering at the University of Texas at Austin, which conducted the test in White Sands, New Mexico, recently at the behest of the U.S. Department of Homeland Security.During the demo, which was first reported by Fox News, the researchers were able to take control of a drone from a distance of about a kilometer, or two-thirds of a mile.

