How to outfox Web sites trying to get you to pay top dollar
Following news that Orbitz is showing pricier hotels to Mac OS users, here are some tips for changing browser settings and other practices to get deals and access you wouldn't normally get on the Web.
So, Orbitz has spilled the beans, well some of them, and says it in essence up-sells to people based on which browser they use.
The site told The Wall Street Journal (subscription required) that it discovered that Mac users tend to pay as much as 30 percent more for hotel rooms. (Well, they are paying a premium for the computer too so it's not that surprising, although $20 to $30 more is significant.) Leveraging that information, Orbitz decided to experiment with displaying pricier hotels in search results to Mac users than to Windows users. Before you get too miffed, Orbitz says that it isn't showing different rates for the same hotel rooms and that user history and location, as well as hotel popularity and promotions play an even bigger part in how the results are displayed. Also, you can just sort results based on price to see unadulterated bargains on top.
Orbitz isn't the only Web site using browser and other user or system footprint information to determine what content or services visitors see. "Sites will use whatever they can glean," says Jeremiah Grossman, chief technology officer at White Hat Security. "The IP address gives location down to the ZIP code. There are geolocation services that can tie an IP address to a particular company or they can tell if you are using your computer at home. There are also differences based on browser. Chrome users are more tech savvy than IE 6 users generally speaking." Armed with this type of information, Web sites adjust ads and offers, and content, accordingly.
Here are some tips for masking your system and hiding your history in order to trick Web sites into giving you better deals or access to restricted content:
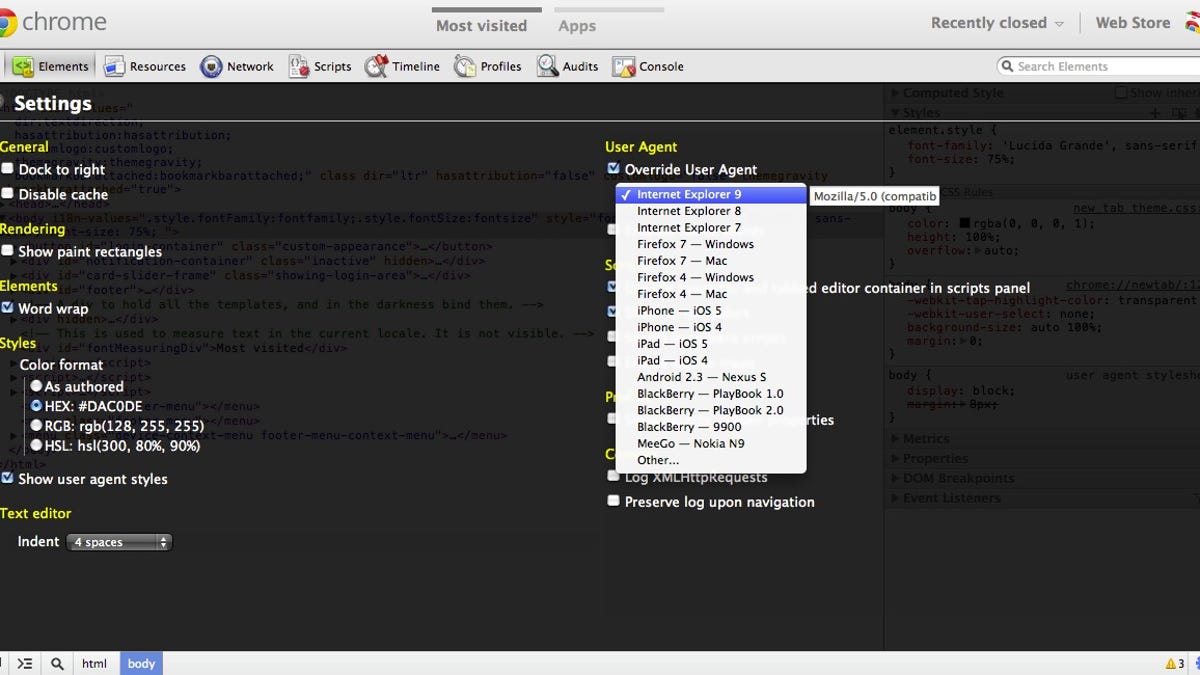
Spoofing your operating system If you want sites to think you use a different operating system than you use, you can modify the User Agent settings in your browser, something developers need to do on a regular basis to test out sites. To do this in Chrome, click wrench tool icon in the upper right corner and then click "Tools" and "Developer Tools." In the black window check "Override User Agent" and select which a browser option for this particular tab. There is similar functionality in Internet Explorer, as well as Safari. And Firefox has a User Agent Switcher add-on that can be used to spoof the platform and version.
However, some sites are still able to determine the true platform despite what the user agent header string in your browser says, according to Grossman. If you are serious about this task you might want to use a virtualized environment such as VMware Fusion, which allows you to run Windows on the Mac. If so, you can have visualized environment for browsing and use the virtualization software to surf in a Windows environment on your Mac.
Appearing as a brand new visitor Some Web sites are so desperate to get your business that they will quote discounted rates if they think you are a brand new customer.
"It's not widely talked about because no one knows precisely what they are doing," Grossman said. To fool the site into thinking they have snared new business you can delete your cookies and stored data, which includes Flash content. Or, if you don't want to delete all the cookies on your machine, which would affect your log-in and other interactions with all sorts of other sites, you can set up multiple browser profiles.
One profile can be specifically used for shopping and dumping the cookies would only affect that profile. To do this in Chrome, you can click the wrench icon in the browser toolbar, select "Settings" and click "Add new user" in the "Users" section. If you want all your settings to be synced to the new account you will have to sign in to Chrome with your Google Account. Otherwise you can skip that step and the settings for the user will be saved only on your computer. This process in IE
It's a bit harder to create multiple profiles in Firefox. You have to go to "Applications/Utilities" and open the "Terminal" application and type in "/Applications/Firefox.app/Contents/MacOS/firefox-bin -p" and press "Return." When the Profile Manager window appears you click "Create Profile" and give it a name. Apparently there is no good way to create multiple browser profiles in Safari, according to this Apple support forum thread.
Modifying your browsing footprints Along the same lines as the new business discounts, some sites will go out of their way to court customers of their rivals with cheaper prices."I've had great success on airlines and insurance sites" by making it appear that the browser has visited competitive Web sites, said Grossman. "I can make it look like I'm a customer of Geico, for instance, when trying to sign up with Esurance."
This technique takes advantage of a CSS (Cascading Style Sheets) history sniffing vulnerability that has been fixed in the current versions of the major browsers, but which can still be secretly exploited by Web sites when visitors are using older browsers, he said. About a third of the Internet population is still use the older browsers, according to Grossman. Basically, JavaScript running on the Web site can distinguish whether your browser has visited specific other sites based on the color of the hyperlink. Content is served up based on what color the hyperlink is. This is all done transparently to the visitor.
"If I want the best deal from Esurance, I'll dump my cookies with the old browser and then go to Geico's site and then visit Esurance," Grossman said.
Getting access to restricted content Then there are the times when you are blocked from accessing fee-based content you really want to see such as New York Times or Wall Street Journal articles (such as the one about Orbitz referred to above) that are behind a paywall. An easy way to get around that is to type the article title into Google Search and then click the link in the search results. And for people who want to get around geographic content restrictions, such as Netflix imposes on downloading of movies outside a particular region, there is a different trick. Using a VPN (Virtual Private Network), or encrypted tunnel, can make it look like your download request is coming from a server in the U.S. instead of a hotel in Australia. In addition to allowing you to bypass content filtering, VPNs -- like HotSpot Shield or ProXPN - can prevent Wifi sniffing and man-in-the-middle attacks.

